-
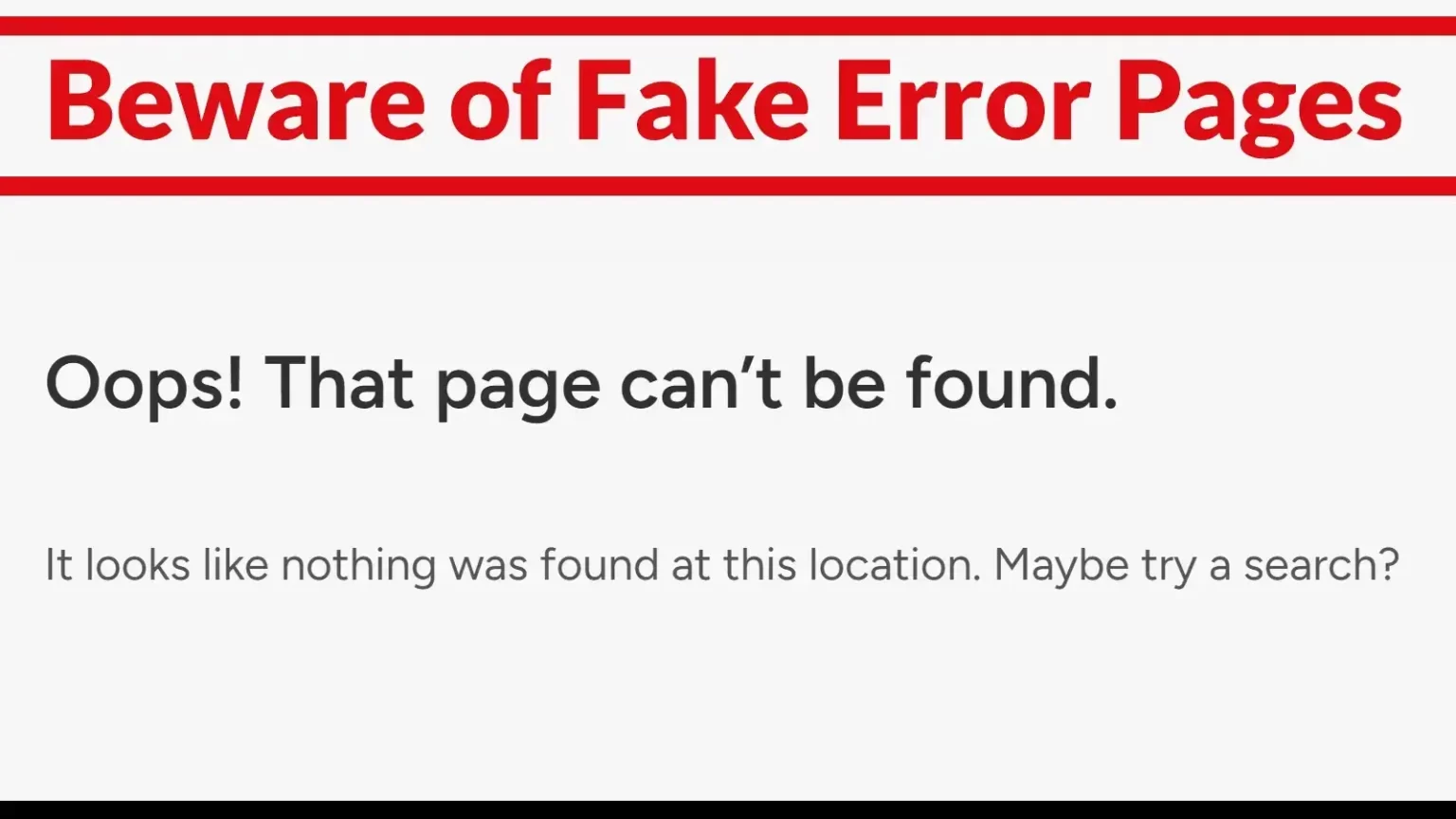
Criminals are concealing harmful computer programs within deceptive “404 error” web pages.
-
The treacherous software targets both Linux and Windows operating systems and proves exceptionally difficult to detect.
-
Users may experience subtle symptoms, such as reduced computer speed and increased energy consumption.
A fresh wave of digital attacks, dubbed Soco404, is exploiting computers to secretly generate cryptocurrency by disguising malicious code within standard “Page Not Found” notifications.
Typically, accessing a broken website link results in a 404 error page. The individuals orchestrating Soco404 are fabricating these error pages. However, concealed within them lies encoded malware – a type of computer program that instructs your machine to mine cryptocurrency (like Monero) on behalf of the attacker.
These counterfeit pages are being hosted on compromised websites, including Google Sites, to appear legitimate. The malware is engineered to operate stealthily on both Windows and Linux-based computers.
Difficult to Spot
Because the malware is integrated into standard web coding, it often bypasses detection by antivirus programs and firewalls. Upon downloading, the malicious program installs itself within the computer’s memory, avoiding writing data to the hard drive, thus minimizing its visibility.
Furthermore, it erases its own traces, camouflages itself as a system process (adopting names like kworker or sd-pam), and disables essential logging functions in Windows, preventing IT personnel from observing its activity.
How They Gain Access
A frequent point of entry involves improperly configured databases – particularly PostgreSQL databases, which many cloud users inadvertently expose to the public internet. The hackers are exploiting a characteristic of PostgreSQL that permits the execution of system commands. This allows them to move horizontally across networks and install mining software on multiple devices.
In some cases, hacked websites based in South Korea are being used to spread different versions of the malware – one specifically for Windows (ok.exe) and another for Linux (soco.sh).
What It Means for You
If you observe a sudden decline in computer speed or an increase in your electricity bill, it could be indicative of this type of attack. Because the malware operates quietly and effectively hides itself, conventional cybersecurity measures may fail to detect it.
Security experts suggest the following precautions:
-
Securing publicly accessible databases.
-
Monitoring your computer for unusual error page downloads.
-
Analyzing CPU usage for unexpected surges.
In conclusion, this attack demonstrates that even seemingly simple error pages can pose a threat if compromised. Exercise caution regarding downloads on your systems – even when the outcome appears benign.