A widespread hacking operation has injected JavaScript cryptocurrency miners into more than 3,500 websites globally. This resurgence of browser-based cryptojacking mirrors tactics formerly employed by services like CoinHive.
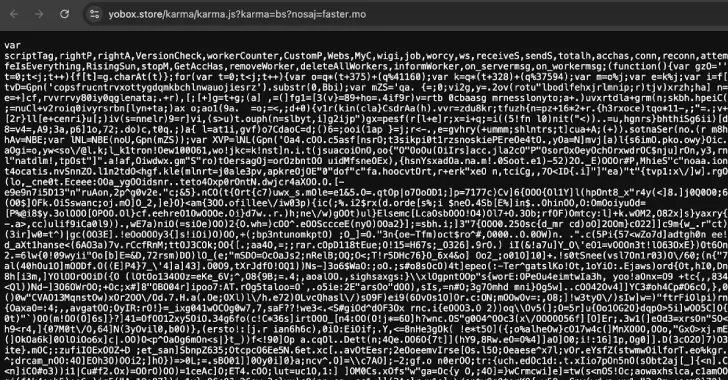
Despite the fact that CoinHive ceased operations after web browser developers implemented safeguards against miner applications, cybersecurity analysts at c/side have uncovered a concealed miner hidden within obfuscated JavaScript code. This stealthy program gauges a device’s processing power and initiates parallel mining operations through background Web Workers, all without triggering user alerts.
Crucially, the malicious code utilizes WebSockets to receive mining instructions from a remote server. This enables the attackers to dynamically adjust the mining intensity depending on the device’s resources, throttling consumption to remain undetected.
“This is a carefully crafted stealth miner, designed to evade detection from both website visitors and security systems,” stated Himanshu Anand, a security researcher, noted.
As a result, unsuspecting users unknowingly contribute their computer’s resources to mine cryptocurrency while browsing the affected websites, effectively turning their devices into clandestine crypto-mining machines without their awareness or authorization. The precise methods used to compromise these websites and inject the in-browser miner are still under investigation.
Further analysis reveals that over 3,500 websites have been compromised in this extensive illicit crypto-mining scheme. The domain hosting the malicious JavaScript miner has also been linked to Magecart credit card skimmers in previous incidents, suggesting that the attackers are attempting to diversify their malicious activities and income streams.
The overlapping use of domains to distribute both cryptocurrency miners and credit card theft tools highlights the threat actors’ proficiency in weaponizing JavaScript and launching opportunistic attacks against unsuspecting website visitors.
“Attackers are now prioritizing stealth over outright resource theft, leveraging obfuscation techniques, WebSockets, and infrastructure reuse to remain undetected,” c/side reported. “Their strategy focuses on sustained, subtle resource exploitation, resembling a digital vampire gradually draining resources over time.”
These findings coincide with the discovery of a separate Magecart skimming campaign targeting e-commerce sites in East Asia operating on the OpenCart content management system. The attackers inject a fraudulent payment form during the checkout process to capture sensitive financial data, including bank account details, before transmitting it to their servers.
Recent client-side and website attacks have manifested in various forms:
- The utilization of JavaScript embeds to exploit the callback parameter associated with a legitimate Google OAuth endpoint (“accounts.google[.]com/o/oauth2/revoke”). This redirects users to obfuscated JavaScript code that establishes a malicious WebSocket connection to a domain controlled by the attacker.
- Direct injection of Google Tag Manager (GTM) scripts into WordPress databases (specifically the wp_options and wp_posts tables). This loads remote JavaScript code that redirects visitors to over 200 spam websites.
- Compromising a WordPress site’s wp-settings.php file to include a malicious PHP script directly from a ZIP archive. This script connects to a command-and-control (C2) server and manipulates the site’s search engine rankings to inject spam content and boost the visibility of malicious websites.
- Injecting malicious code into a WordPress site theme’s footer PHP script, causing browser redirects.
- Employing a fake WordPress plugin, named after the infected domain, to evade detection. This plugin activates only when search engine crawlers are detected, serving spam content designed to manipulate search engine results.
- Distributing backdoored versions of the WordPress plugin Gravity Forms (affecting versions 2.9.11.1 and 2.9.12) through the official download page in a supply chain attack. This modified plugin contacts an external server to retrieve additional malicious code and creates a new administrator account, granting the attacker complete control over the compromised website.
“If successfully installed, the modified code will prevent updates to the plugin and attempt to communicate with an external server to download further malicious components,” RocketGenius, the developers of Gravity Forms, announced.
“Successful execution of this additional code allows the attacker to create an administrative account. This creates a backdoor, potentially leading to remote access, unauthorized code injection, manipulation of existing administrator accounts, and access to sensitive WordPress data.”