Global crypto trading platform Bybit has reported a significant security incident. A sophisticated cyberattack resulted in the unauthorized removal of digital assets valued at over $1.5 billion. This breach involved an Ethereum cold wallet (an offline storage system), and is currently considered the largest single cryptocurrency theft to date.
According to Bybit’s official statement released via X (formerly Twitter), “During a routine transfer of funds from our ETH multisig cold wallet to a designated hot wallet, a manipulation occurred. The user interface presented the correct address, however, the underlying smart contract logic was altered by a carefully orchestrated attack.” The transaction details are publicly available.
This allowed the threat actors to seize control of the compromised Ethereum cold wallet and transfer the funds to an unknown destination, according to Bybit’s official statement.
Bybit’s CEO, Ben Zhou, assured users, via social media, that all remaining cold wallets are secure. The exchange has also confirmed that the incident has been formally reported to the relevant law enforcement agencies.
Although Bybit has not officially confirmed the perpetrators, blockchain analysis firms like Elliptic and Arkham Intelligence are pointing toward the notorious Lazarus Group, a North Korean state-sponsored hacking organization. This incident surpasses previous major crypto heists, significantly exceeding the losses from the Ronin Network breach ($624 million), the Poly Network attack ($611 million), and the BNB Bridge exploit ($586 million).
Crypto investigator ZachXBT has drawn a connection “on-chain” between the Bybit breach and the recent Phemex hack that occurred in late May.
The Lazarus Group is recognized as a persistent and highly skilled threat actor, responsible for numerous cryptocurrency thefts used to fund the North Korean government. Google’s threat analysis team has previously described North Korea as “arguably the world’s leading cyber criminal enterprise.”
Chainalysis estimates that in 2024 alone, the group has stolen approximately $1.34 billion in crypto assets across 47 separate incidents, accounting for approximately 61% of all cryptocurrency theft during this period. The Lazarus Group has been observed targeting a wide range of critical infrastructure as well.
According to Mandiant, a Google-owned cybersecurity firm, “The rise in cryptocurrency heists stems from the combination of high financial rewards, the inherent difficulties in attributing malicious actions, and the relative unfamiliarity of many organizations with the intricacies of cryptocurrency and Web3 technologies.” The company released this warning last month.
Update
Bybit has released an updated statement regarding the event, saying that on February 21, 2025, at approximately 12:30 p.m. UTC, unusual activity was detected within one of its Ethereum (ETH) Cold Wallets during a planned and routine fund transfer.
The exchange stated in an official announcement that “The transfer was a scheduled movement of ETH from our ETH Multisig Cold Wallet to our Hot Wallet.”
“Regrettably, the transaction was the subject of manipulation using a sophisticated attack to alter the smart contract logic. This allowed the attacker to seize control of the ETH Cold Wallet, resulting in a transfer of over 400,000 ETH and stETH, collectively valued at over $1.5 billion, to an unidentified external address.”
TRM Labs has also linked this security incident to the Lazarus Group with “high confidence,” citing “considerable overlap observed between addresses controlled by the Bybit hackers and addresses previously tied to North Korean thefts,” including those affecting Phemex, BingX, and Poloniex.
Check Point Research commented, “The Bybit incident illustrates a new phase in attack methodologies, including sophisticated techniques that manipulated user interfaces. The attackers used user interface manipulation rather than relying on protocol mechanics and successfully compromised a highly secure institutional multisig setup.”
The cybersecurity firm also noted that this attack highlights the potential for threat actors to manipulate legitimate transactions through the Gnosis Safe Protocol’s execTransaction function, and that “multisig cold wallets are not guaranteed secure if signers are deceived, therefore increased focus must be placed on supply chain security and user interface protection.”
An in-depth analysis published by Elliptic over the weekend described a repeated pattern in Lazarus Group’s laundering process where the stolen tokens are converted into a native blockchain asset such as Ether to work around freezing attempts.
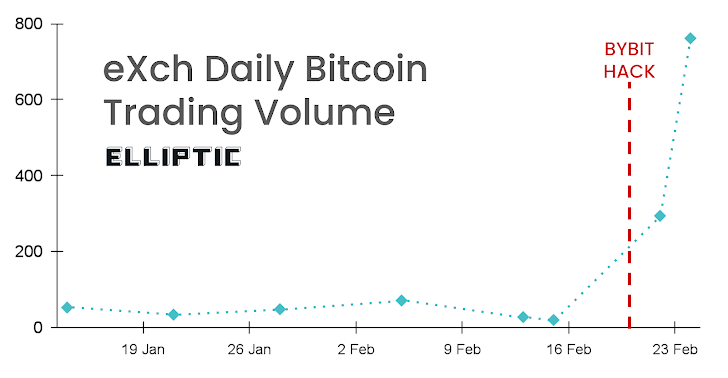
The company reported that the Bybit hack followed this pattern, with stolen tokens being exchanged for Ether within minutes of the theft, adding that funds were distributed to 50 separate wallets within a two-hour timeframe and were further transferred to exchanges such as eXch to be exchanged for bitcoin.
“North Korea’s Lazarus Group is the most advanced and resource-rich launderer of cryptoassets in the world, and they continuously adjust their techniques to avoid identification and seizure of stolen funds,” said Elliptic.
Elliptic also pointed out that the eXch exchange has allowed North Korean actors to launder illicit funds through cryptoasset swaps without requiring identification, and that over $75 million was laundered through eXch from Bybit alone.
eXch, however, denies that the funds stolen from Bybit were laundered on their exchange, stating that they are “NOT laundering money for Lazarus/DPRK” and that “an insignificant part of funds processed by us from the ByBit hack in an isolated case will be donated to various open-source initiatives dedicated to privacy and security both inside and outside crypto space.”
“They are definitely laundering funds stolen by the DPRK from Bybit – this is visible on the blockchain,” Dr. Tom Robinson, co-founder and chief scientist at Elliptic, told The Hacker News.
“Over $75 million in stolen funds has passed through eXch. They are trying to conceal it, and the total figure may be higher. Moreover, this is not the first instance of cryptoassets linked to DPRK’s hacks being sent through eXch.”
(This story was updated after initial publication to include more recent information and further revise the total cryptocurrency stolen during the incident.)