Cyber correspondent, BBC World Service

Getty Images
Cybercriminals, allegedly affiliated with the North Korean government, have reportedly succeeded in converting a substantial portion, at least $300 million (equivalent to £232 million), of the unprecedented $1.5 billion in cryptocurrency stolen during a recent digital heist into funds that are virtually impossible to recover.
This notorious group of cyber thieves, identified as the Lazarus Group, executed the massive digital token theft by breaching the security of the ByBit crypto exchange approximately two weeks prior.
Ever since the incident, a tense pursuit has been underway to monitor and prevent the hackers from successfully converting the stolen cryptocurrency into readily accessible, usable currency.
According to expert analyses, this infamous hacking collective is purportedly operating almost continuously, around the clock, potentially funneling the illicitly obtained funds into the regime’s programs for military advancement.
Dr. Tom Robinson, a co-founder of Elliptic, a cryptocurrency investigation firm, stated that “Each passing moment is critical for the hackers who are diligently trying to obscure the money trail, and they are demonstrating remarkable sophistication in their methods.”
Dr. Robinson further emphasized that, among all the criminal entities involved in cryptocurrency activities, North Korea exhibits the highest level of expertise in laundering digital currency.
“It is plausible to envision an entire team dedicated to this operation, utilizing automated tools and drawing upon years of accumulated experience. Their activity patterns suggest that they take only brief pauses each day, potentially working in shifts to expedite the conversion of cryptocurrency into liquid cash.”
Elliptic’s assessment aligns with ByBit’s estimation that approximately 20% of the stolen funds have now “disappeared,” implying a minimal likelihood of their recovery.
The United States and its allies have consistently accused North Korea of orchestrating numerous cyberattacks over recent years with the intention of financing the regime’s military and nuclear development endeavors.
On February 21st, the cybercriminals infiltrated one of ByBit’s vendor partners, enabling them to covertly modify the digital wallet address to which 401,000 Ethereum crypto coins were being transferred.
Unbeknownst to ByBit, the funds, which they believed were being directed to their own digital wallet, were instead rerouted entirely into the hands of the hackers.

Getty Images
Ben Zhou, the Chief Executive Officer of ByBit, has assured his clientele that none of their individual funds were compromised during the security breach.
The company has subsequently replenished the stolen cryptocurrency holdings by securing loans from its investors, and is currently, in Zhou’s words, “engaged in a battle against Lazarus”.
Through ByBit’s Lazarus Bounty program, members of the public are being encouraged to assist in tracking the movement of the stolen funds and facilitating their potential freezing.
Since all crypto transactions are publicly accessible and recorded on a distributed ledger, the blockchain, it is possible to monitor the movement of the stolen funds as they are being transferred by the Lazarus Group.
If the hackers make an attempt to utilize a mainstream cryptocurrency exchange service to convert the stolen crypto assets into traditional currencies such as US dollars, these cryptocurrency holdings can be flagged and frozen by the service provider if they are identified as being linked to criminal activities.
To date, a total of 20 individuals have collectively received more than $4 million in rewards for their successful identification of $40 million worth of the stolen cryptocurrency, and for alerting crypto firms who subsequently blocked these suspect transfers.
However, industry experts express a degree of pessimism regarding the likelihood of recovering the remaining stolen funds, given North Korea’s renowned capabilities in hacking and the laundering of digital assets.
According to Dr. Dorit Dor, a cybersecurity expert from Check Point, “North Korea operates as a highly isolated and closed economic system, which has fostered the creation of a successful industry specializing in both hacking and laundering. They are seemingly unconcerned with the negative perception associated with engaging in cybercriminal activities.”
A contributing factor to the challenge of fund recovery is the varying levels of cooperation exhibited by different cryptocurrency exchanges.
The crypto exchange known as eXch has faced accusations from ByBit and other entities for allegedly failing to adequately prevent the cybercriminals from cashing out their ill-gotten gains.
It is reported that over $90 million has been successfully moved through this particular exchange.
However, Johann Roberts, the elusive owner of eXch, has contested these claims through email correspondence.
Roberts acknowledges that eXch did not initially halt the transactions, citing an ongoing dispute with ByBit and claiming uncertainty regarding the origins of the cryptocurrency holdings as definitively linked to the cyberattack.
Roberts maintains that eXch is now cooperating with the investigation, while also arguing that mainstream companies’ practices of identifying crypto customers are in conflict with the privacy and anonymity that cryptocurrency is supposed to provide.
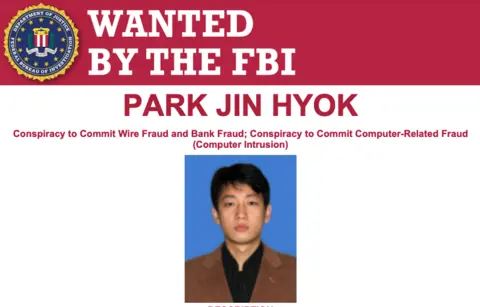
FBI
While North Korea has consistently denied any association with the Lazarus Group, it is widely considered to be the only nation globally that utilizes its hacking capabilities primarily for financial gain.
Initially, the Lazarus Group’s hacking activities targeted traditional financial institutions, but over the past half-decade, they have shifted their focus to attacking companies operating in the cryptocurrency space.
Compared to traditional financial institutions, the cryptocurrency industry exhibits weaker security measures and fewer established mechanisms to effectively prevent the laundering of illicit funds.
Recent cyberattacks that have been attributed to North Korea include:
- The 2019 breach of UpBit, resulting in losses of $41 million.
- The theft of $275 million in cryptocurrency from the KuCoin exchange (a substantial portion of the funds was subsequently recovered).
- The 2022 Ronin Bridge attack, in which hackers absconded with $600 million in cryptocurrency.
- The 2023 attack on Atomic Wallet, resulting in the theft of approximately $100 million in cryptocurrency.
In 2020, the United States authorities included North Korean individuals, suspected of being affiliated with the Lazarus Group, on its list of “Cyber Most Wanted” criminals. However, the odds of these individuals ever being apprehended remain exceptionally slim, unless they venture outside the borders of their country.