The rapid advancement of generative AI and the sophistication of LLMs are fueling a surge in cyberattacks and the deployment of malicious bots. While basic bots were once the domain of less-skilled cybercriminals, AI now empowers advanced threat actors to craft extremely complex and evasive malware.
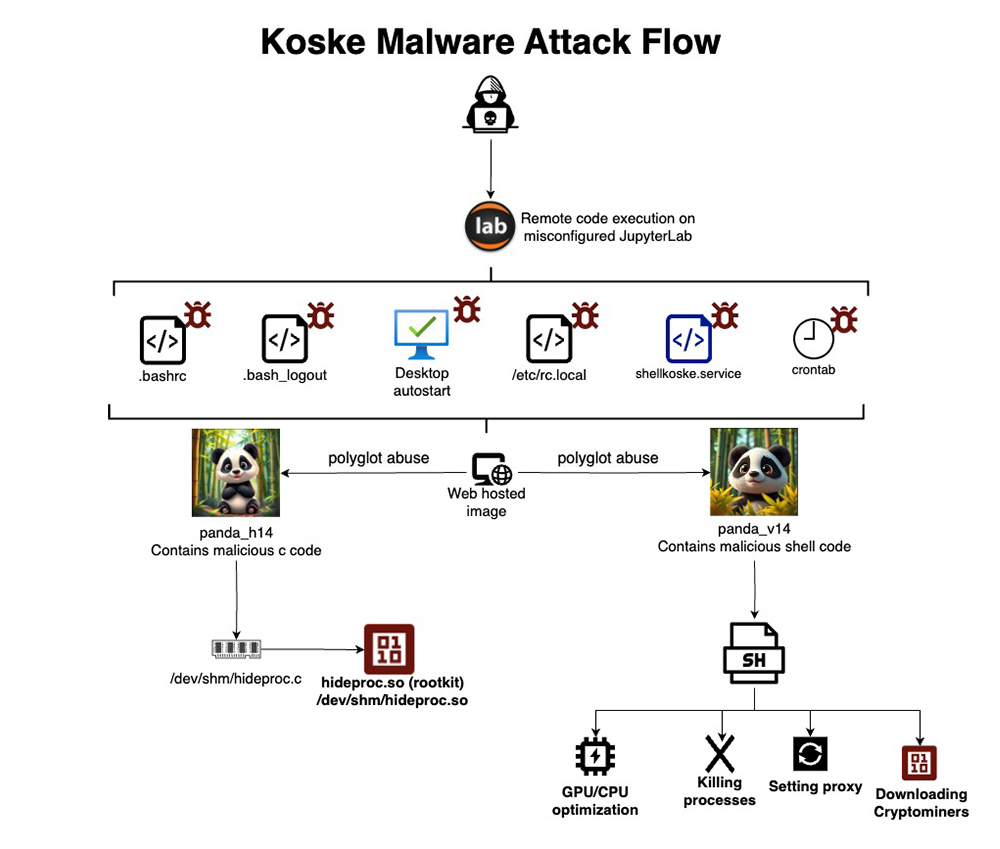
A newly discovered malware strain, dubbed Koske, exemplifies this trend. It disguises itself within seemingly harmless panda images located on platforms such as freeimage, postimage, and OVH images. These images are then used to compromise Linux-based computer systems. Koske cleverly integrates image files with rootkit capabilities and dynamically adjusting crypto-mining routines, establishing a stealthy and persistent backdoor on targeted systems.
Koske’s key innovation lies in its use of polyglot files A file capable of being interpreted in multiple ways, contingent on the application or context in which it’s used.. Specifically, JPEG images that appear to show innocent pandas, but actually embed hidden shell scripts and C programming code.
A file capable of being interpreted in multiple ways, contingent on the application or context in which it’s used.. Specifically, JPEG images that appear to show innocent pandas, but actually embed hidden shell scripts and C programming code.
Upon execution, the file appears as a regular image. However, behind the scenes, it triggers malicious commands to deploy cryptocurrency miners. These miners are carefully optimized for both CPU and GPU processing, targeting a range of 18 different cryptocurrencies, including Monero, Ravencoin, Nexa, Tari, and Zano. Attackers initially gain entry by exploiting unprotected or poorly configured JupyterLab installations.
If communication with the hacker’s Command & Control (C2) infrastructure is disrupted, the malware autonomously troubleshoots the connection. It attempts to re-establish contact using tools such as curl and wget over TCP. The malware also manipulates iptables rules, alters DNS settings, searches for new proxy servers from GitHub lists, and brute-forces proxy configurations – all in an effort to re-establish communication with the command server.
To maximize profitability, Koske dynamically switches between different mining pools and cryptocurrencies if one becomes unproductive. Additionally, Koske employs hidden rootkits to conceal its files, processes, and presence from typical security software. It achieves persistence through scheduled cron jobs, modifications to .bashrc and .bash_logout scripts, and the creation of dedicated systemd services. Its network module is advanced in its proxy detection capabilities, leading to robust resilience under varying network environments – indicative of sophisticated, potentially AI-driven logic.
Researchers have observed modular code, thoroughly commented programming logic, and robust defensive coding practices, suggesting that Koske was likely created with the aid of large language models (LLMs).
Prior Security Incidents
In a separate incident, over 3,500 websites were compromised by hidden scripts designed to mine Monero (XMR) tokens. This form of malware operates covertly, avoiding password theft or data encryption, instead, using the processing power of website visitors’ browsers to mine Monero cryptocurrency, without their knowledge or consent.