Introducing QuantumShield-BC: Fortifying Blockchains Against Quantum Threats
As quantum computing advances, its potential to compromise existing cryptographic techniques becomes increasingly apparent. Traditional methods like RSA and ECC, the backbone of blockchain security, are vulnerable to quantum attacks, particularly Shor’s algorithm. This reality necessitates the development of blockchain architectures capable of resisting future quantum threats. QuantumShield-BC answers this call, providing robust protection for decentralized systems in the face of quantum advancements.
QuantumShield-BC: Secure Blockchain for the Quantum Era
QuantumShield-BC is a novel framework designed to safeguard blockchain technologies against quantum computer-based attacks. It achieves this by integrating cutting-edge post-quantum cryptography (PQC) with quantum key distribution (QKD), ensuring security and long-term resilience. With the increasing reliance on blockchain for secure transactions, digital identity, and decentralized applications (DApps), quantum-resistant mechanisms are no longer a distant concern but a pressing need.
Classical encryption, the foundation of current blockchain security models, faces the risk of being easily broken by quantum computers. QuantumShield-BC proactively addresses this vulnerability by incorporating lattice-based post-quantum digital signatures, which can be seamlessly integrated into smart contracts. This integration lowers the barrier to adoption while simultaneously ensuring signature security, even in a quantum adversarial setting. To further bolster security, Quantum Key Distribution (QKD) establishes secure peer-to-peer communication channels, mitigating the risk of eavesdropping and man-in-the-middle attacks.
Traditional blockchain systems relying on deterministic pseudo-random number generators (PRNGs) are susceptible to attacks that exploit nonce prediction in digital signatures. QuantumShield-BC mitigates this risk by introducing quantum random number generation (QRNG), providing cryptographically secure random values for transaction hashes, smart contract execution, and the consensus mechanism. This significantly enhances entropy and security by introducing unpredictable randomness.
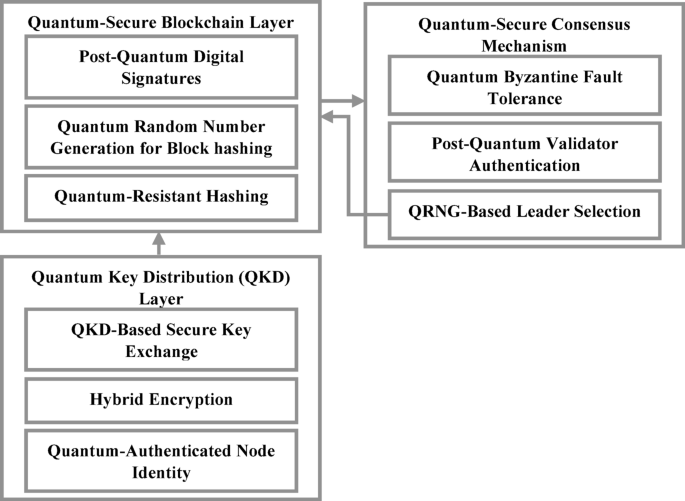
System Architecture Overview
Figure 1: System architecture of QuantumShield-BC with PQC, QKD, QRNG, and Q-BFT integration for secure blockchain operations.
QuantumShield-BC secures each transaction and innovatively replaces standard proof-of-stake (PoS) and proof-of-work (PoW) models with a Quantum-enhanced Byzantine Fault Tolerance (Q-BFT) consensus layer, extending transactional protection to the consensus mechanism. Validator nodes utilize post-quantum cryptographic authentication, preventing adversaries from forging signatures or manipulating the consensus process. The framework also incorporates post-quantum secure multi-party computation (MPC) to fortify node selection and block validation against both classical and quantum-based cyberattacks.
QuantumShield-BC represents a paradigm shift in blockchain security, blending the robustness of classical cryptography with quantum-safe innovations. By combining encryption with lattice-based digital signatures, QKD-secured communication, QRNG-enhanced randomness, and a quantum-resistant consensus protocol, it creates a next-generation, tamper-proof blockchain ecosystem. As quantum technology continues to evolve, the need for a quantum-secured, decentralized system intensifies. QuantumShield-BC offers a forward-looking solution, safeguarding the integrity of blockchain applications across diverse sectors in an era where quantum adversaries pose a growing threat.
Transaction Workflow
Figure 2: Workflow diagram of QuantumShield-BC depicting end-to-end transaction processing with PQC-based signing, QKD communication, QRNG-driven leader selection, and Q-BFT consensus.

The QuantumShield-BC workflow illustrates the complete lifecycle of a blockchain transaction protected against quantum threats. The process starts with a user-initiated transaction, digitally signed using post-quantum cryptography. This transaction is then securely transmitted across blockchain nodes using quantum key distribution (QKD). Validators authenticate the transaction using lattice-based signatures, followed by QRNG-based leader selection to ensure an unbiased consensus initiation. The Quantum Byzantine Fault Tolerance (Q-BFT) protocol executes for multi-party consensus. Upon reaching agreement, the block is finalized and appended to the blockchain, and the user receives a confirmation, completing the secure and quantum-resilient transaction flow.
Key Notations
Table 1: Notations used in the QuantumShield-BC framework for quantum-secure blockchain operations. (Table data would be displayed here)
Quantum-Secure Blockchain Layer: Defense Against Quantum Adversaries
QuantumShield-BC creates a quantum-safe layer on top of the blockchain, shielding it from quantum threats across all layers: transaction validation, block generation, and ledger management. This layer provides the option to replace traditional cryptographic methods with post-quantum digital signatures and integrate quantum-safe hash functions, boosted by quantum random number generation (QRNG) to amplify entropy. These enhancements fortify the blockchain against key stealing, signature forgery, and entropy-based attacks that may become feasible with the advent of quantum computers.
Digital signatures are crucial for verifying transaction authenticity and preventing manipulation. Unlike classical cryptographic schemes like RSA or ECDSA, which are vulnerable to Shor’s algorithm, QuantumShield-BC adopts PQC algorithms such as CRYSTALS-Dilithium or Falcon for signing and verifying transactions. A transaction’s validity (V(T)) is determined by verifying the post-quantum digital signature (Sk) of the transaction’s hash (H(T)) using a quantum-resistant verification function (VerifyPQ).
Blockchain security also depends on secure block generators that maintain data integrity and immutability. In QuantumShield-BC, each block is linked to the previous one using a quantum-resistant hashing function, such as SPHINCS+ or Keccak, providing resistance to Grover’s search algorithm. The hash of a block (H(Bn)) is computed using a post-quantum secure hash function (HashPQ) based on the hash of the previous block (Bn-1), the transactions it contains (Tn), and a digital signature of the block (Sn).
A fundamental weakness of classical blockchains lies in their reliance on deterministic pseudo-random number generators (DPRNGs), which are susceptible to entropy prediction attacks. QuantumShield-BC addresses this by leveraging quantum random number generation (QRNG) to inject high-entropy randomness into cryptographic operations such as block generation and nonce generation in smart contracts. The quantum entropy function (RQ) is defined by the Shannon entropy formula, ensuring roll results are genuinely random and free from weak state seeds.
QuantumShield-BC employs a quantum-resistant Merkle tree for secure ledger storage. Instead of a traditional Merkle tree, which relies on hash-based proofs vulnerable to quantum attacks, QuantumShield-BC utilizes a post-quantum Merkle tree where each node is signed using a lattice-based digital signature. This ensures transaction integrity against quantum adversaries.
QuantumShield/QuantumShield-BC distinguishes itself as a tamper-resistant and robust decentralized ledger by combining post-quantum digital signatures, hash hardening algorithms, and QRNG-based entropy. These enhancements ensure the blockchain remains operational and resilient against emerging quantum-computing attack vectors, making QuantumShield-BC the future of decentralized, secure applications.
Quantum Key Distribution (QKD) for Secure Communication
QuantumShield-BC enhances blockchain security by employing Quantum Key Distribution (QKD) for secure peer-to-peer communication, protecting cryptographic keys exchanged between blockchain nodes from quantum attacks. Traditional key-exchange mechanisms, such as RSA and Diffie-Hellman, are vulnerable to Shor’s algorithm. QKD, however, allows secure generation and transmission of cryptographic keys based on quantum states, making eavesdropping and key compromise infeasible.
Figure 3: Quantum key distribution (QKD) process flow illustrating secure key exchange between blockchain nodes using quantum states and classical reconciliation.

Protected by the no-cloning theorem and superposition in quantum mechanics, QKD facilitates intercept-resilient cryptographic key exchange. QuantumShield-BC uses the BB84 protocol to exchange a key between sender and receiver nodes via quantum state-encoded, polarized photons. If an eavesdropper attempts to intercept the quantum channel, the quantum state collapses, alerting the communicating parties.
After successful key exchange, a secure symmetric encryption channel is established between blockchain nodes, ensuring the privacy and security of transmitted blockchain data. QuantumShield-BC also supplements QKD with post-quantum cryptographic algorithms. QKD guarantees key confidentiality, and post-quantum key encapsulation mechanisms (KEM), such as Kyber and FrodoKEM, provide hybrid security for blockchain data exchange. This hybrid encryption protects against vulnerabilities in one security layer by ensuring the other remains secure. Validator nodes in the blockchain network are authenticated using a quantum-secure key exchange method, defending against Sybil and identity spoofing attacks. A QKD-authenticated identity hash is generated for each validator node, ensuring consensus and block validation occur only among quantum-authenticated nodes.
By utilizing QKD for secure key exchange and integrating it with hybrid encryption schemes and QKD-authenticated node validation, QuantumShield-BC mitigates risks associated with classical key exchange protocols and secures the blockchain against both classical and quantum attacks, establishing a secure communication channel for future decentralized networks.
Practical Considerations for Deployment
While QKD provides theoretically unbreakable secure key exchange, practical implementations face challenges. High hardware costs for quantum photon sources, detectors, and synchronization systems, coupled with channel loss over long distances, limit scalability, especially in fiber-optic or free-space links. QuantumShield-BC addresses these issues with modular integration supporting hybrid PQC-KEM mechanisms to supplement QKD in situations where its deployment is not feasible. Future enhancements will explore satellite-based QKD or trusted node relays to mitigate distance-related losses and increase the system’s practicality.
Quantum-Secure Consensus Mechanism: Enhancing Security with Quantum BFT
QuantumShield-BC enhances blockchain security with a quantum-secure consensus, utilizing post-quantum cryptographic algorithms within a Byzantine Fault Tolerance (BFT) framework. Classic consensus schemes like PoW and PoS are susceptible to quantum attacks. QuantumShield-BC’s proposed Q-BFT-based protocol ensures secure block validation and transaction verification, even in a quantum environment.
Figure 4: Quantum byzantine fault tolerance (Q-BFT) consensus flowchart showing validator authentication, QRNG-based leader selection, and multi-party consensus execution.

In QuantumShield-BC, each validator node verifies transactions with a post-quantum cryptographic signature before contributing to the consensus, preventing malicious parties from forging validator credentials. The consensus decision function aggregates validator signatures, appending the block to the blockchain only if a sufficient number of quantum-authenticated validators approve it. QuantumShield-BC implements quantum-resistant threshold cryptography to ensure block finalization requires participation from a sufficiently large number of validators, maintaining decentralization and thwarting quantum adversaries. The framework uses QRNG for unbiased leader election, making leader selection unpredictable and non-manipulatable.
For enhanced security, QuantumShield-BC integrates a hybrid consensus validation scheme with quantum multi-party computation (QMPC), enabling secure transaction validation among multiple validators without revealing sensitive cryptographic information. By combining QRNG with PQC-threshold signatures, QRNG leader selection, and QMPC consensus validation, QuantumShield-BC is secure against both classical and quantum adversarial attacks, allowing decentralized blockchain systems to achieve tamper-proof security in the quantum era and positioning it as a next-generation blockchain consensus framework.
Implementation of the QuantumShield-BC Prototype
The development of the QuantumShield-BC prototype involves a phased approach, progressively integrating quantum-safe blockchain components. Alongside post-quantum cryptography (PQC), the prototype incorporates quantum key distribution (QKD), quantum-secure consensus algorithms, and quantum random number generation (QRNG) to bolster blockchain immunity against quantum attacks. Critical security concerns, such as transaction verification, block creation, consensus assurance, and secure peer-to-peer communication, are addressed at each stage.
The initial phase focuses on integrating post-quantum digital signatures, transitioning from classical RSA and ECC signatures to post-quantum signatures. QuantumShield-BC uses lattice-based cryptographic methods like CRYSTALS-Dilithium and Falcon for signing transactions, ensuring secure transactions. This prevents non-quantum-resistant signatures from being added to the blockchain.
The second phase focuses on securing node communication using QKD, enabling nodes to share encryption/decryption keys for blockchain communication. This addresses vulnerabilities in traditional key exchange schemes like Diffie-Hellman and RSA. If an eavesdropper intercepts the key, they alter the quantum state, immediately alerting the communicating parties.
To ensure tamper-proof block generation, QuantumShield-BC employs quantum-resistant hashing to link blocks within the blockchain. The block hash calculation uses SPHINCS+ or Keccak, which are resistant to Grover’s algorithm attacks. This ensures data cannot be changed and is resistant to quantum attacks.
Future developments will focus on implementing Quantum Byzantine Fault Tolerance (Q-BFT), a post-quantum consensus protocol that supersedes traditional PoS and PoW mechanisms. Validator nodes must prove their identity with quantum-secure signatures before joining the consensus, preventing unauthorized participation.
To achieve fair leadership selection in consensus, Quantum Random Number Generation (QRNG) is implemented to eliminate bias and predictability during leader selection. QuantumShield-BC relies on QRNG for fair and tamper-free leader election, free from pseudo-randomness sources.
The final stage involves deploying the QuantumShield-BC prototype on a testbed to evaluate its security and performance against quantum attacks. The security of transaction verification, consensus, and block generation is validated through quantum attack simulations using quantum computing simulators (e.g., IBM Qiskit or Google Cirq). The integrity of the global blockchain is validated through a multi-party consensus verification function, preventing non-quantum-secure transactions from entering the blockchain.
By incorporating PQC digital signatures, QKD, quantum-secure hashing, and QRNG-based consensus, the QuantumShield-BC prototype provides an ultra-resilient and tamper-proof blockchain platform. The systematic evolution and integration of quantum-safe technology into a blockchain ensures it remains operational, scalable, and robust against emerging quantum threats, paving the way for a future quantum-safe blockchain 2.0.
Proposed Algorithms
This section details the key algorithms underpinning QuantumShield-BC, each designed to address a specific system component, including transaction authentication, secure key exchange, quantum-safe consensus, and randomness generation. Together, these algorithms provide end-to-end quantum resilience, facilitating secure, scalable, and tamper-proof blockchain operations against emerging quantum computational threats.
Algorithm 1: Post-Quantum Digital Signature Algorithm
Secures blockchain transactions using post-quantum digital signatures. It starts by hashing the transaction data and generating a signature with a private key using a post-quantum algorithm. The signature is attached to the transaction and verified with the corresponding public key, ensuring authenticity, tamper-proofing, and resistance to quantum attacks.
Algorithm 2: Quantum Key Distribution (QKD) Algorithm
Enables secure key exchange between blockchain nodes using quantum key distribution. The sender transmits quantum states, and the receiver measures them using random bases. Through classical communication, both parties compare bases and retain matching bits to form a raw key. After error correction and privacy amplification, a final secure key is established, ensuring tamper-proof communication against quantum adversaries.
Algorithm 3: Quantum-Resistant Hashing Algorithm
Generates a quantum-resistant hash for a blockchain block using post-quantum cryptographic functions. The algorithm concatenates the current block data with the previous block’s hash as input. A secure hash function, such as SPHINCS+ or Keccak, is applied to produce a tamper-proof hash, ensuring ledger integrity and immutability.
Algorithm 4: Transaction Validation Algorithm
Performs transaction validation using post-quantum cryptographic techniques. The algorithm extracts the transaction and its digital signature, computes the transaction’s hash, and verifies the signature using the sender’s public key. If verification succeeds, the transaction is accepted; otherwise, it is rejected, ensuring only authentic and quantum-secure transactions enter the blockchain.
Algorithm 5: QRNG-Based Nonce and Randomness Generation Algorithm
Generates quantum-secure random numbers using a quantum random number generator (QRNG). The process begins by producing a sequence of quantum bits, which are measured to obtain raw entropy. A randomness extraction function is applied to refine the output, providing true, unpredictable randomness used for nonce generation, leader selection, and other critical blockchain processes.
Algorithm 6: QRNG-Based Leader Selection Algorithm
Selects a consensus leader using quantum-generated randomness. A random number is generated via a quantum random number generator (QRNG) and mapped to a validator index by taking the modulus with the total number of validators. If the selected validator is active, it is assigned as the leader, ensuring fair, unpredictable, and tamper-proof leader selection.
Algorithm 7: Quantum Byzantine Fault Tolerance (Q-BFT) Consensus Algorithm
Establishes consensus using the Quantum Byzantine Fault Tolerance (Q-BFT) mechanism. Each validator verifies transactions using post-quantum signatures and broadcasts its result. The system aggregates validator votes and compares them against a predefined threshold. If the number of valid votes meets or exceeds this threshold, consensus is achieved and the block is approved; otherwise, consensus fails and is retried.
Algorithm 8: Post-Quantum Multi-Party Consensus Verification Algorithm
Performs post-quantum multi-party consensus verification among validators. Each validator independently verifies transaction signatures using post-quantum cryptography. The results are securely shared and aggregated using quantum-secure multi-party computation. If all verifications are successful, consensus is confirmed. Otherwise, the transaction is rejected, ensuring tamper-resistant validation across distributed nodes in a quantum-secure blockchain environment.
Algorithm 9: Block Finalization and Addition Algorithm
Finalizes and appends a validated block to the blockchain. It first checks whether consensus has been achieved. If valid, the block data is hashed using a post-quantum secure hash function and linked to the previous block. The finalized block is then added to the blockchain and broadcast to the network, ensuring integrity, immutability, and resistance to quantum-based tampering.
Algorithm 10: Quantum-Aware Network Security Algorithm
Secures validator communication using quantum-aware techniques. It begins by establishing a key via quantum key distribution, followed by validator authentication using post-quantum signatures. All messages are encrypted using the QKD-derived key. Replay and Sybil attacks are mitigated through QRNG-generated nonces and identity checks, ensuring quantum-resilient, authenticated, and tamper-proof communication across blockchain nodes.
Performance Evaluation Metrics
The performance of QuantumShield-BC is assessed through several essential criteria to measure its security, efficiency, and scalability against quantum threats. The evaluation considers transaction validation latency, consensus throughput, cryptographic entropy, and benchmark quantum resistance, ensuring QuantumShield-BC maintains high-speed operation while using post-quantum cryptographic (PQC) primitives, QKD, Quantum Byzantine Fault Tolerance (Q-BFT), and QRNG.
Transaction validation time, measuring the time to validate a transaction using post-quantum digital signatures, is a primary metric. The validation time (Tv) includes the time to compute a post-quantum signature (TSign) and the time to verify the signature (TVerify). While lattice-based signatures introduce computational overhead compared to ECC, PQC schemes with minimal latency are selected to achieve the most efficient QuantumShield-BC.
Consensus throughput, the number of transactions handled per second while maintaining security against quantum adversaries, is another essential metric. The throughput of the Q-BFT consensus mechanism (TQ-BFT) is defined as the number of transactions validated (NT) divided by the total running time for reaching a decision (TC). Quantum-Secure Multi-Party Computation (QMPC) ensures secure transaction validation while minimizing the computational overhead caused by post-quantum cryptographic primitives.
QuantumShield-BC balances computational efficiency and post-quantum security when selecting specific PQC algorithms. CRYSTALS-Dilithium and Falcon schemes were considered as digital signatures, both finalists in the NIST post-quantum cryptography standardization process. Falcon was chosen for consensus authentication in the prototype due to its fast signature verification time, while Dilithium was selected for transaction signing where signature size is less critical.
Entropy assessment of QRNG-based blockchain functions evaluates the randomness quality applied to leader selection, nonce generation, and cryptographic key generation. Shannon entropy is used to determine the quantum entropy value (RQ), where higher entropy implies better randomness, increased security for cryptographic keys, and greater unpredictability in blockchain operations.
The quantum resistance of blockchain transactions is analyzed by simulating Shor’s Algorithm to compare the resistance of classical versus post-quantum cryptography. QuantumShield-BC uses PQC primitives like Kyber, FrodoKEM, and SPHINCS+ that are secure against quantum decryption.
Network overhead due to QKD-based encryption is also measured. QuantumShield-BC is designed to be lightweight and maintain overall communication efficiency as QKD key exchange rates improve and unnecessary quantum-state transmissions are suppressed. A key metric is the block confirmation time (TB), the time taken for the network to agree upon a new block. This is calculated by dividing the sum of the time for communication among validators (TComm) and the time for quantum-safe random value generation (TQ-Rand) by the number of validators involved (VC).
Key Novelties of QuantumShield-BC
QuantumShield-BC offers a uniquely integrated quantum-secure blockchain architecture incorporating post-quantum digital signatures, secure communication through QKD, QRNG-based leader election, and a new Q-BFT consensus protocol within a single framework. In contrast to earlier efforts focused on individual layer security (PQC or QKD only), QuantumShield-BC is an integrated, layered solution with protocol-level modularity and consolidated quantum cryptographic implementations across the transaction, network, and consensus layers.
A primary novelty is the use of post-quantum cryptographic (PQC) signatures instead of classical digital signatures, securing transactions against quantum adversaries. Existing blockchain systems relying on ECDSA, a cryptographic algorithm vulnerable to Shor’s algorithm, are at risk. Including lattice-based signature schemes like CRYSTALS-Dilithium and Falcon makes the framework resistant to quantum-enabled key compromise. These signatures maintain blockchain security against the post-quantum threat by enabling efficient transaction validation while ensuring computational infeasibility for signature forgery.
It also introduces quantum key distribution (QKD) to safely transport node-to-node communication over single-mode fiber, preventing eavesdropping or interception of encryption keys. Based on quantum mechanics, QKD ensures eavesdropping on cryptographic keys disturbs their quantum state, making such efforts detectable. This allows blockchain nodes to securely exchange encryption keys, creating a quantum-resistant peer-to-peer communication mechanism resistant to man-in-the-middle (MITM) attacks.
The Quantum Byzantine Fault Tolerance (Q-BFT) consensus mechanism strengthens blockchain validator fault tolerance. Sybil attacks are mitigated as Q-BFT, using post-quantum digital signatures and multi-party secure computation, ensures only quantum-authenticated validators can form a consensus. This prevents adversaries with quantum capabilities from controlling the network and maintains decentralized trust.
QRNG provides the unpredictability needed for cryptographic processes, ensuring block generation, nonce selection, and smart contract execution are entirely random. Classical PRNGs make blockchain systems vulnerable to replay attacks and nonce manipulations. QRNG, based on quantum mechanical principles, offers a genuinely unpredictable entropy source, guaranteeing tamper-evident cryptographic randomness immune to deterministic weaknesses intrinsic to classical PRNGs.
QuantumShield-BC also provides secure blockchain storage with quantum-resistant hashing techniques, maintaining immutability in the face of quantum attacks. Traditional hashes, like SHA-256, are vulnerable to Grover’s algorithm. The framework uses hash-based digital signatures such as SPHINCS+ and quantum-resistant hashing algorithms such as Keccak, ensuring blockchain ledger data is secure and unalterable by quantum computers.
The leader selection mechanism is generally vulnerable to predictability attacks. QuantumShield-BC addresses this using QRNG for leader selection, ensuring a random and immutable selection of validators. This prevents adversarial influence from private information, ensuring safety and transparency in blockchain governance.
The framework incorporates a hybrid cryptographic scheme that merges QKD and post-quantum key encapsulation mechanisms (PQC-KEM), including Kyber and FrodoKEM. This hybrid encryption preserves security even under a QKD compromise, making QuantumShield-BC more resistant against classical and quantum threats.
Finally, QuantumShield-BC is resilient to quantum-enhanced replay attacks. Classical blockchains use nonce verification to prevent duplicate transactions, but quantum computers can bypass validation with incorrect timestamps. Integrating QRNG ensures each transaction uses a truly quantum-generated atom to generate the next nonce, preventing replay of old transactions. This provides robust protection against double-spending and duplication attacks, even in a quantum computing environment.
In summary, QuantumShield-BC combines post-quantum cryptography, quantum key distribution, QRNG, and Q-BFT consensus to protect against quantum attacks on all parts of the blockchain. It serves as a benchmark for secure, decentralized, and tamper-proof blockchain ecosystems, offering out-of-the-box quantum resilience compared to traditional blockchains requiring cryptographic upgrades.