A cunning cryptojacking scheme is exploiting a common Windows tool, the Character Map (charmap.exe), to avoid detection by Windows Defender and secretly mine cryptocurrency on affected computers.
This attack, initially observed around late August of 2025, takes advantage of trusted system files to introduce a specially designed cryptomining program directly into the computer’s active memory. This bypasses standard antivirus software that relies on identifying known malicious file signatures, while also making it harder to trace the attack.
Security experts have discovered this new method of cryptojacking, a cyberattack where perpetrators commandeer a computer’s resources to mine digital currencies without the owner’s permission.
Attackers introduce cryptomining programs or scripts that consume a computer’s CPU or GPU power. This leads to higher electricity bills and reduced computer performance for the victims, while the attackers illegally profit.
Unlike ransomware attacks, where victims are directly demanded money, cryptojacking quietly steals resources over a long timeframe. This makes it more challenging to notice and slower to fix.
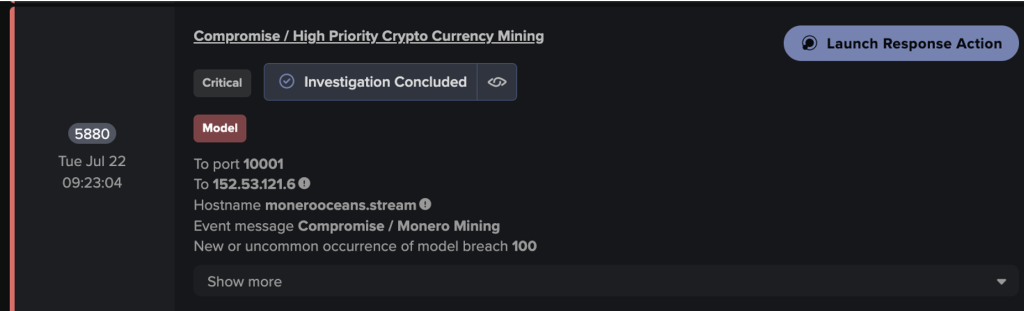
Darktrace identified and stopped a cryptojacking attempt aimed at a retail and e-commerce client.
The infection begins with carefully crafted phishing emails that include a malicious shortcut file disguised as a PDF document.
When opened, the shortcut triggers the Windows PowerShell to retrieve a hidden downloader program from a remote online location. This downloader then places two key components of the attack in the user’s AppData folder:
- AutoIt Loader: This small program unencrypts the cryptominer and inserts it into a running instance of
charmap.exe, the standard Windows Character Map tool. - Mining Binary: A specifically designed 64-bit cryptominer that is designed to connect to a distant mining pool using TCP port 3838.
By making use of charmap.exe, the malicious software avoids introducing a suspicious, unknown program onto the hard drive, thereby bypassing the behavior-based detection systems of Windows Defender.
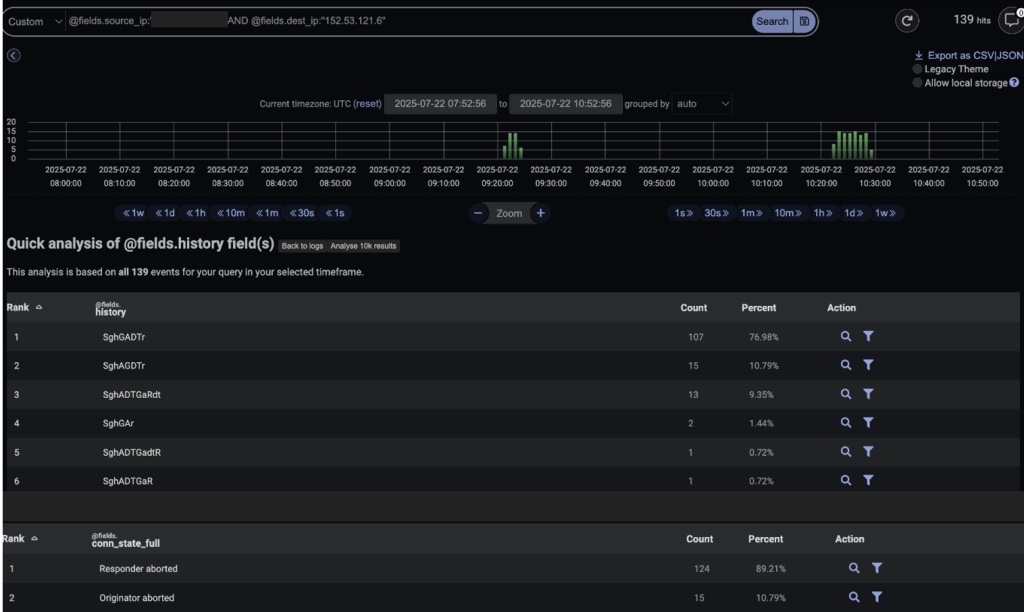
The combination of IP address and destination port (152.53.121[.]6:10001) has previously been identified by open-source intelligence providers as being associated with cryptomining activity.
After the cryptominer is injected, the Character Map continues to perform its usual function. The running cryptominer operates hidden from normal user activity.
Evasion and Persistence
Darktrace’s Cyber AI Analyst started an independent review of this activity and was successful in linking the individual attack events, from the initial PowerShell connection attempts through the subsequent connections to the cryptomining server.
Rather than treating these incidents as isolated events, the Cyber AI Analyst could understand the entire scope of the attack, delivering extensive awareness.

To ensure persistence, the attack generates a scheduled task known as “WindowsCharMapUpdater” that restarts the loader when a user logs in.
It also adds a DLL file to the local application data folder, abusing the legitimate werfault.exe process through DLL side-loading, which ensures the miner is automatically restarted after system restarts or process shutdowns.
The range of victims varies from small businesses to larger enterprise environments, with the most frequent occurrences in the healthcare and education industries.
Compromised computers show increased CPU and GPU utilization—often surpassing 80%—resulting in sluggish performance, overheating issues, and higher electricity usage.
Given the high value of cryptocurrencies, criminals view cryptojacking as a relatively safe and potentially very profitable activity. By taking advantage of trusted Windows programs like Character Map, they can secretly run their mining operations for extended periods.
For larger organizations, the increased energy costs can reach thousands of dollars each month, in addition to the decrease in productivity due to slower computer performance.
Mitigations
Traditional antivirus software using signature-based detection struggles against these fileless injection techniques, highlighting the necessity for security systems that are based on recognizing abnormal activity.
Across over 130 connection attempts, the Darktrace SOC has verified that all of them were successfully stopped, indicating no connections successfully established.
Security teams should monitor for unusual PowerShell commands, rare parent-child process connections related to the Character Map, and any outgoing connections to known mining pool locations.
Implementing application allow-listing for essential system files and requiring strict rules for running PowerShell scripts are both helpful to prevent similar attacks.
It is essential that organizations maintain up-to-date detection methods in order to identify subtle changes from normal system activities.
These strategies, combined with detailed endpoint monitoring and intelligence sharing about threats, allow security teams to successfully handle evolving cryptojacking attacks and protect vital systems from unauthorized mining activity.
Find this Story Interesting! Follow us on LinkedIn and X to Get More Instant Updates.