Darktrace reveals a new form of malware that exploits the Windows Character Map to conduct cryptomining, emphasizing the need to guard against sneaky attacks hiding within commonly used software functions.
Cybersecurity specialists at Darktrace, a firm specializing in AI-powered security solutions, have uncovered a complex attack where everyday Windows applications are secretly hijacked to mine for digital currency. The investigation was spearheaded by Cyber Analyst Keanna Grelicha and Threat Research Lead Tara Gould, who then reported their discoveries to Hackread.com.
This type of cyberattack, known as cryptojacking, involves using a victim’s computer resources to generate cryptocurrency for the attacker, resulting in increased electricity consumption and reduced system performance.
According to Darktrace’s official report, their security systems identified and thwarted a cryptojacking attempt on July 22, 2025, targeting a customer in the retail and e-commerce sector.
The initial alert was triggered by unusual activity: the device was utilizing a novel PowerShell user agent. The attack stood out because an “obfuscated AutoIt loader” was employed to distribute the malicious software, identified as NBMiner, a technique not previously observed.
Malware Analysis
Upon closer inspection, it was discovered that the attackers used sophisticated scripting to download and execute the NBMiner malware directly within the computer’s active memory. This initial script was intentionally obscured with multiple layers of encoding, making reverse engineering and analysis significantly challenging.
The malware proceeded to inject itself into a legitimate, trusted Windows process: the Character Map application (charmap.exe). To evade detection, the malware included checks to determine if programs like Task Manager were running and to verify if Windows Defender was the sole security solution present on the system.
Once operational, the cryptominer attempted to establish a connection with a cryptomining pool identified as gulf.moneroocean.stream to initiate mining operations. By camouflaging itself within a legitimate Windows process, the malware could potentially escalate its privileges and remain undetected. This approach complicates detection because it circumvents standard security protocols and anomaly detection methods.
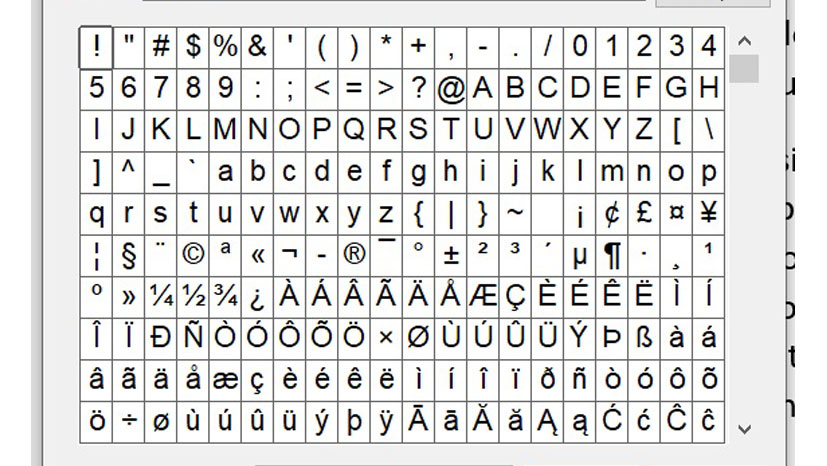
For context, the Windows Character Map is an integrated Windows tool that enables users to browse and insert special characters, symbols, and characters from different languages not typically accessible via standard keyboard layouts.
The Need for Enhanced Security Measures
Sadly, cryptojacking continues to be a prevalent threat because of its ability to scale across numerous devices. Although these attacks may seem minor, they can result in data privacy breaches and substantial financial losses due to energy consumption from the illicit use of computational resources.
In the reported incident, Darktrace’s autonomous response mechanism efficiently neutralized the threat by preventing the infected device from linking to the attacker’s infrastructure, effectively stopping the attack at its earliest stages. This demonstrates the significance of deploying advanced security protocols that proactively impede threats, rather than simply detecting them.
Jason Soroko, a Senior Fellow at Sectigo, a Scottsdale, Arizona-based entity specializing in certificate lifecycle management (CLM), offered insights on the latest development, emphasizing that organizations should “regard modern cryptojacking as an early warning signal of intrusion, not merely a harmless inconvenience.”
He highlighted that such attacks could conceal broader objectives, such as stealing credentials and conducting network reconnaissance. According to Soroko, the key to reducing threat detection times lies in gaining insights into the behavior of scripts, processes, and network connections, rather than relying solely on a database of known vulnerabilities.