Cybersecurity experts have recently uncovered details about two separate malware operations. These malicious campaigns are actively exploiting weaknesses and configuration errors within cloud infrastructure to install cryptocurrency mining software.
Cloud security specialists at Wiz and Aqua have designated these threat groups as Soco404 and Koske, respectively.
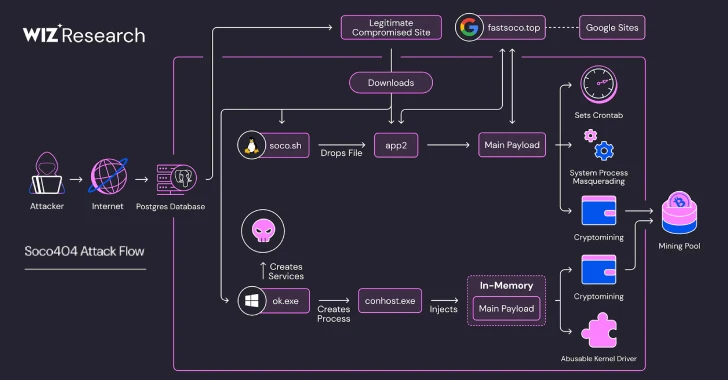
According to Wiz researchers Maor Dokhanian, Shahar Dorfman, and Avigayil Mechtinger, Soco404 “is engineered to infect both Linux and Windows operating systems, utilizing malware specifically tailored to each platform.” They further explained that “the group employs process masquerading, a technique to conceal illicit activities by disguising them as routine system processes.”
The name Soco404 stems from the attackers’ method of embedding malicious code within counterfeit 404 error pages hosted on websites constructed using Google Sites. Google has since deactivated these fraudulent sites.
Wiz suggests that the Soco404 campaign, which has a history of targeting vulnerable Apache Tomcat services with easily guessed credentials, as well as susceptible Apache Struts and Atlassian Confluence servers through the Sysrv botnet, is likely a component of a larger network of cryptocurrency scams, encompassing deceptive cryptocurrency trading platforms.
The latest iteration of the Soco404 campaign has also been observed targeting publicly accessible PostgreSQL databases. The attackers are also exploiting compromised Apache Tomcat instances to host malicious programs designed for both Linux and Windows environments. Furthermore, a legitimate Korean transportation website was compromised and used for delivering malware.
Upon gaining initial access, the attackers leverage PostgreSQL’s COPY … FROM PROGRAM SQL command. This command is abused to execute arbitrary system commands on the compromised server, enabling remote code execution.
Wiz researchers stated that “the Soco404 attacker appears to be systematically scanning for exposed services, attempting to exploit any available entry point.” They further emphasized that “their use of a diverse array of tools, encompassing Linux utilities like wget and curl, alongside Windows-native tools such as certutil and PowerShell, underscores an opportunistic approach.”
On Linux-based systems, a compact dropper script is immediately executed within the system’s memory. This script downloads and initiates a subsequent stage of malicious code. Simultaneously, the script takes steps to eliminate competing cryptocurrency miners, with the objective of maximizing illicit profits. It also attempts to limit forensic analysis by overwriting logs linked to cron and wtmp.
The payload deployed in this second phase is a binary file that acts as a loader for the cryptocurrency miner. It achieves this by connecting to an external domain (“www.fastsoco[.]top”) which is hosted on Google Sites.
The attack sequence for Windows systems involves an initial post-exploitation command to download and execute a Windows-based binary file. Similar to its Linux counterpart, this file functions as a loader and incorporates both the miner and the WinRing0.sys driver. The latter is employed to gain NT\SYSTEM level privileges.
In addition, the malware attempts to halt the Windows event logging service and initiates a self-deletion command in an effort to avoid detection.
Wiz concluded that “rather than depending on a single technique or operating system, the attacker adopts a broad strategy, deploying any tool or method available within the target environment to deliver their payload.” This flexible approach is indicative of a widespread, automated cryptomining campaign focused on achieving maximum reach and persistence across a diverse range of targets.
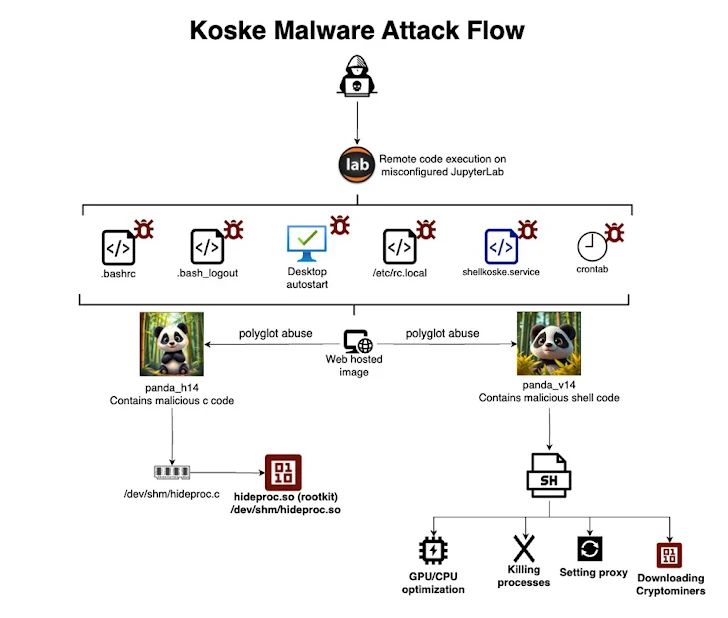
The discovery of Soco404 coincides with the emergence of a novel Linux-targeted threat known as Koske. It is suspected that Koske’s development involved assistance from a large language model (LLM). The malware uses seemingly harmless images of pandas to facilitate its distribution.
The Koske attack begins by exploiting a misconfigured server, such as JupyterLab, to install various scripts retrieved from two JPEG image files. One of these scripts is a C-based rootkit, which uses LD_PRELOAD to conceal malicious files associated with the malware. Another script ultimately downloads cryptocurrency miners onto the compromised system. Both the rootkit and the cryptocurrency miners are executed directly in memory, reducing their footprint on the disk.
Koske’s ultimate objective is the deployment of cryptocurrency miners optimized for both CPU and GPU processing. These miners exploit the computational capabilities of the infected host to mine a selection of 18 different cryptocurrencies, including Monero, Ravencoin, Zano, Nexa, and Tari, among others.
Aqua researcher Assaf Morag explained that “these images are polyglot files, with malicious payloads appended at the end. When these files are downloaded, the malware extracts and executes the malicious segments within memory, enabling it to bypass antivirus protection.”
Morag clarified, “This technique is not steganography, but rather polyglot file abuse, or malicious file embedding. It utilizes a valid JPG file that contains malicious shellcode at the end. Only the final bytes of the image file are downloaded and executed, making it a sneaky form of polyglot abuse.”