A software developer specializing in blockchain technology, residing in Russia, experienced a significant financial setback, losing approximately $500,000 worth of cryptocurrency. This loss was attributed to the unwitting installation of a harmful extension designed for the Cursor AI code editor. The developer was seeking a legitimate extension to enhance code readability through Solidity syntax highlighting but mistakenly downloaded a fraudulent version.
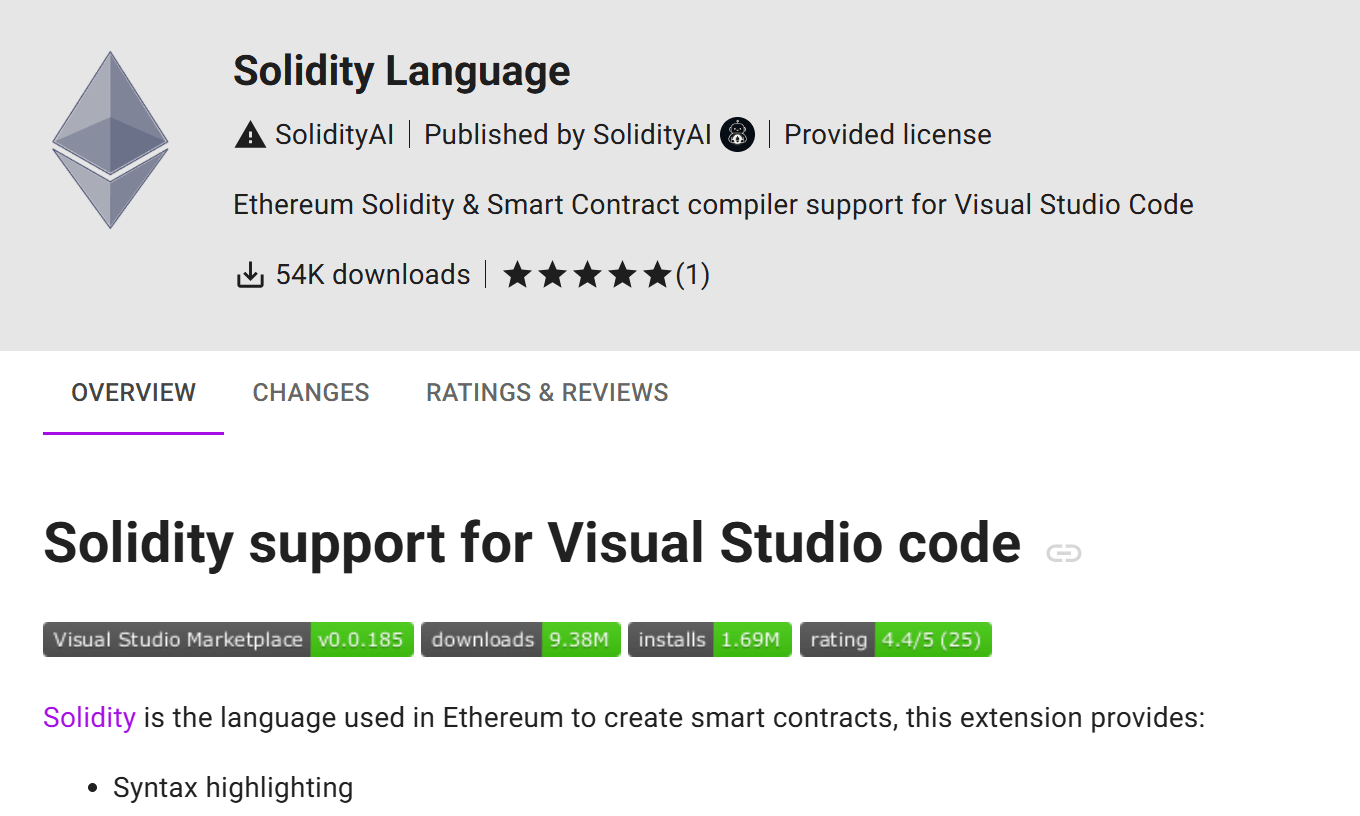
The developer’s search within the Cursor AI browser extension marketplace for “solidity” led to the selection of an extension labeled “Solidity Language,” boasting 54,000 downloads. However, this extension proved to be a counterfeit, with malicious actors having replicated the description from the authentic extension (which had 61,000 downloads) to create a deceptive copy. The counterfeit extension achieved a higher ranking in search results due to the platform’s ranking algorithm. Despite having fewer initial downloads, a more recent update date (June 15, 2025) compared to the original (May 30) elevated its position in the search listings.
Instead of providing syntax highlighting, the rogue extension initiated the download of a malicious PowerShell script from a remote server, subsequently installing the ScreenConnect remote access software. Following this, a data-stealing Trojan was deployed. The compromised extension proceeded to gather sensitive information from various sources, including web browsers, email applications, and cryptocurrency wallets.
After the initial malicious extension was identified and removed on July 2, 2025, the attackers released a new iteration bearing the same name as the authentic one – “solidity.” They even replicated the developer’s name. While the developer names appear visually identical at first glance, the legitimate package originates from “juanblanco,” whereas the malicious version is attributed to “juanbIanco” (note the capitalized “I”). The font employed by Cursor AI renders the lowercase “l” and uppercase “I” virtually indistinguishable.
Consequently, the search results displayed two seemingly identical extensions: a legitimate one with 61,000 downloads and a malicious counterpart that had amassed a staggering 2 million downloads.
Source: SecureList