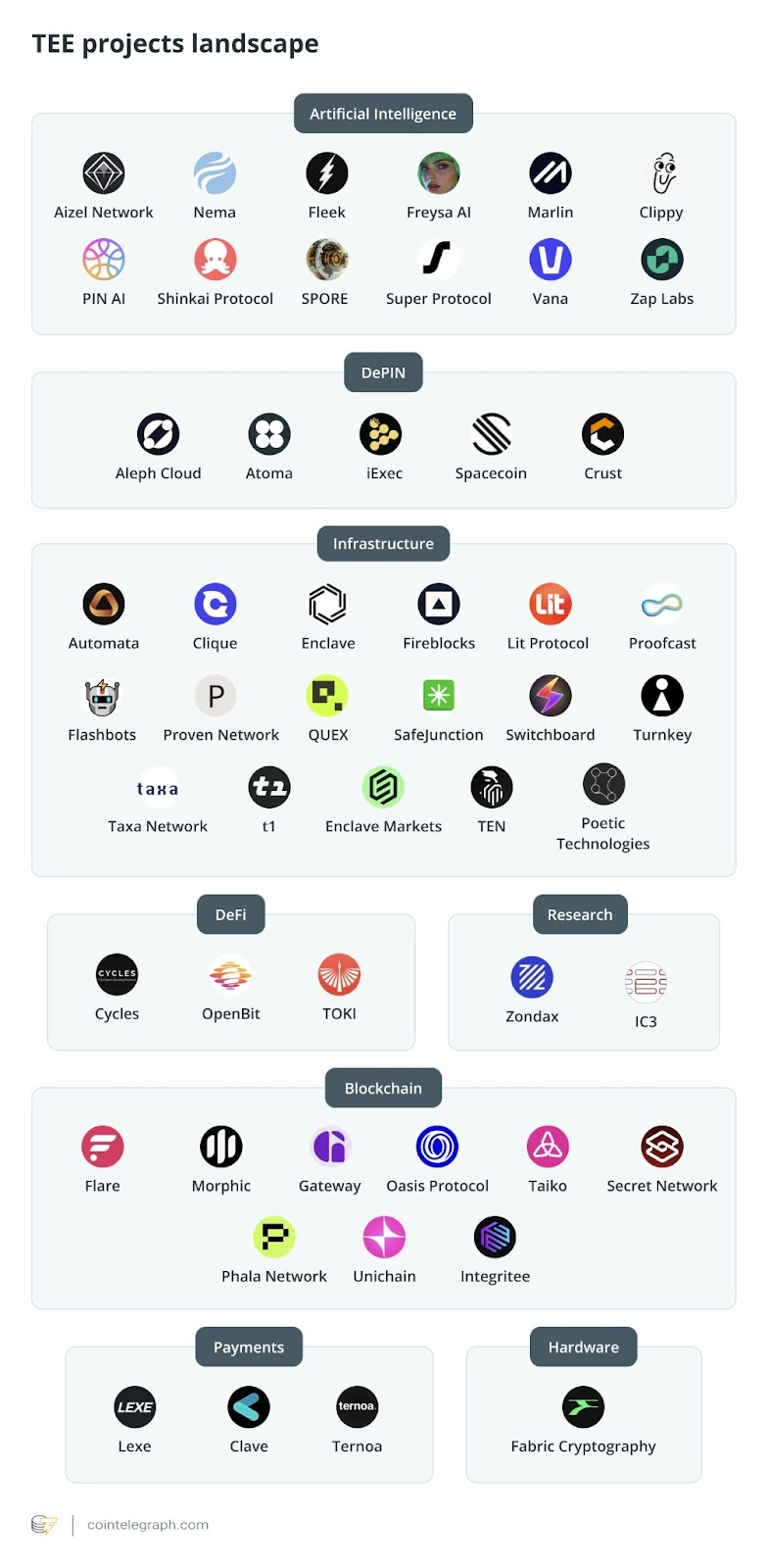
As interest surges in methods to scale and secure blockchain technology, hardware-based approaches are attracting attention. Trusted Execution Environments (TEEs) are increasingly important in blockchain, evolving from simple privacy tools to systems that boost scalability and enable safe off-chain processing. Currently, over 50 development teams are exploring TEE-based blockchain projects. This piece, brought to you by Cointelegraph Research, dives into the underlying tech of TEEs within blockchain environments and explores vital applications of the technology.
How TEEs Function Within Blockchains
While most blockchain systems depend on cryptography and decentralized networks for security, TEEs offer a unique approach: hardware-level assurance.
A Trusted Execution Environment acts as an isolated and secure zone within a processor. Its design ensures data and code remain confidential and unaltered during operation. This secure enclave shields data from the wider operating system and can prove its operations to external parties through remote attestation.
The process involves the CPU measuring the Trusted Computing Base (TCB) – including boot firmware, the operating system kernel, and the binaries of applications. This measurement is then stored within secure hardware registers. After that, the measurement is signed using a private attestation key that is baked into the CPU itself. This signed measurement becomes a cryptographic attestation report which a remote verifier can examine to confirm the authenticity and integrity of the enclave.
Utilizing this hardware-based trust for confidential smart contract operations means blockchain nodes require processors with a TEE. Typically, this applies to nodes responsible for validating transactions, generating blocks, and handling off-chain tasks. In a layer-1 setting, consensus nodes continue to replicate an encrypted version of each smart contract’s state on the global ledger.
Each node using a TEE is responsible for decrypting, executing, and re-encrypting every transaction. This hardware requirement introduces a trade-off: stronger privacy versus a potentially smaller validator set. Requiring specific hardware can limit the number of individuals who can run nodes. However, the remote attestation features offered by TEEs compensate partially for the extra trust that is required.
An alternative approach is a layer-2 structure. In this scenario, TEE computations aren’t secured via distributed consensus, but rather through a dispute resolution process, similar to rollups. This method employs a comparable encryption pipeline to an L1 configuration, but it can enhance scalability. However, many layer-2 solutions forfeit contract interoperability because operations occur on different machines. This means that smart contracts are prevented from directly interacting with one another.
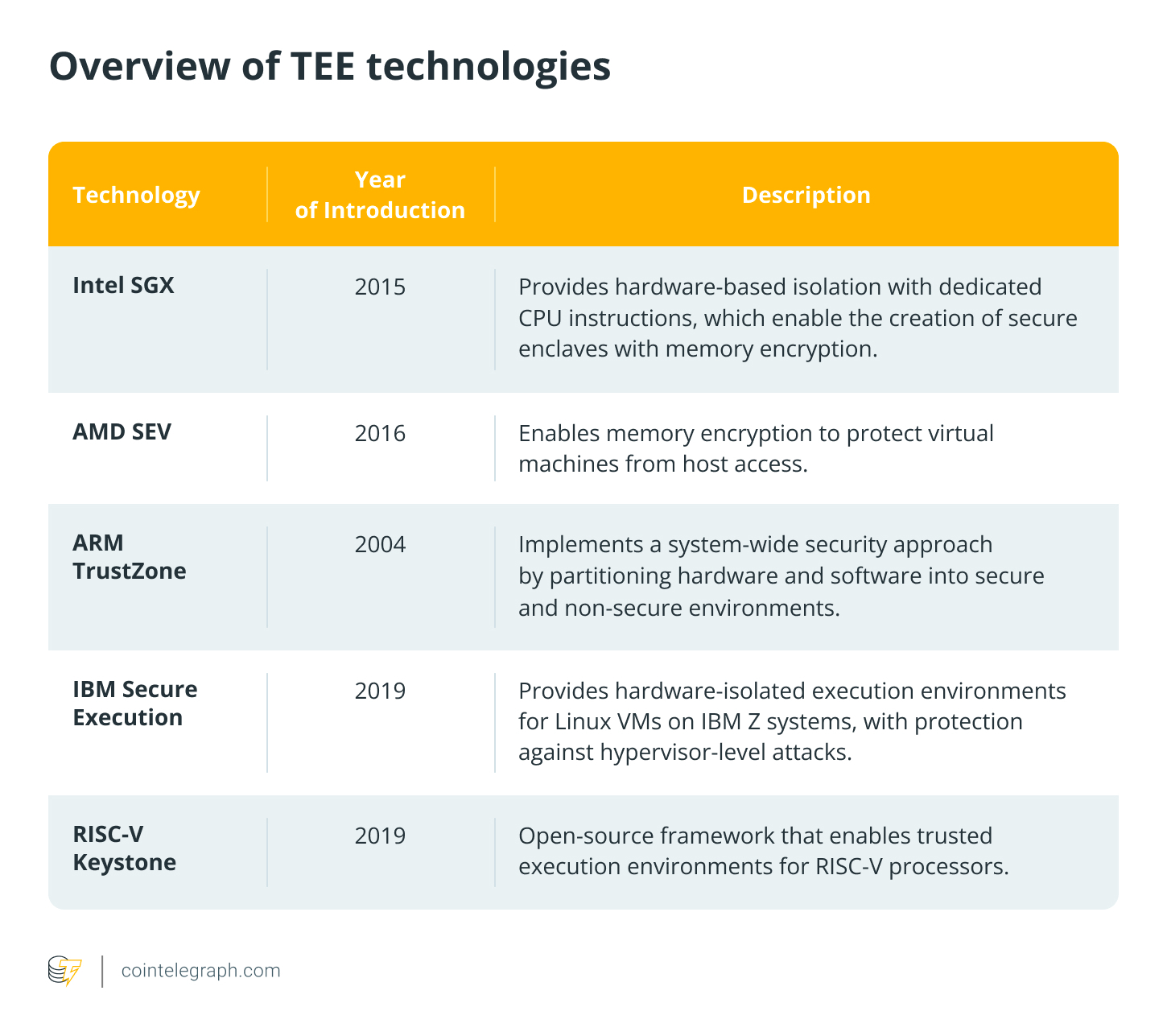
TEEs utilize standard asymmetric cryptography to secure function calls and the code of smart contracts. Before being submitted to the blockchain, function calls are encrypted using the TEE’s public key, then decrypted and executed within the enclave.
Secret Network, using the Cosmos SDK and Intel SGX, was the first blockchain to facilitate private smart contracts via TEEs. Secret Contracts empower developers to build confidential DeFi apps, masking contract logic, inputs, outputs, and state, with the exception of addresses. It also allows the creation of Secret Tokens, where balances and transaction histories are private and visible only to owners or authorized smart contracts.
Potential Weaknesses of Trusted Execution Environments
The execution of private smart contracts relies on the trustworthiness of the TEE hardware manufacturer. While a large company like Intel is unlikely to risk its reputation with a targeted attack on blockchain systems, Intel’s Management Engine (IME), an independent system integrated into most Intel CPUs since 2008, has faced multiple serious vulnerabilities throughout the years.
TEE vendors could face government pressure to introduce backdoors, comply with surveillance demands, or provide access to encrypted data under national security laws. Unintentional vulnerabilities can also compromise a TEE’s security. For instance, the Plundervolt attack took advantage of Intel’s dynamic voltage interface to trigger computational errors within SGX enclaves. This let attackers bypass integrity checks and extract keys and secrets from encrypted memory.
Secure Smart Contract Execution With TEEs
To support privacy-preserving DApps, smart contracts must execute in a way that keeps both the processing logic and data confidential. To read and run protected smart contract code, TEEs must access decryption keys.
If these keys are ever compromised, an attacker could decrypt previously stored smart contract data. To counteract this, Trusted Execution Environments utilize distributed key management. This splits key control across multiple trusted nodes and rotates short-term keys frequently to minimize the impact of any potential security breach.
Ekiden was among the first to develop such a system, establishing a foundation for similar models across other blockchains. The most sensitive keys are controlled by the KMC (key-management committee), which is comprised of the most trusted nodes, through threshold cryptography. The committee’s shares are proactively reshared to rotate who holds each share. In parallel, worker nodes hold short-lived keys with limited access tied to specific tasks.
These keys are issued by the KMC for each contract and expire at the end of every epoch. To acquire a key, a worker node must first prove its legitimacy to the KMC through secure channels. Each KMC member then generates a key share using a pseudo-random function and sends it to the node, which rebuilds the complete key after collecting enough shares.
If a KMC node is compromised, access can be revoked through governance, and the node will be excluded from future epochs. This reduces the potential impact of a breach, though it does not eliminate it entirely. When a confidential contract is deployed, its enclave generates a new public key and broadcasts it on the blockchain alongside the contract code and the encrypted initial state.
Users calling the contract will retrieve this key to encrypt their inputs before submitting them to the compute node. For authentication, the node provides a signing key tied to the enclave through attestation when it starts up.
Other Applications of TEEs in Blockchains
Beyond enabling private smart contract execution, TEEs can significantly improve blockchain scalability and efficiency. TEE-enabled nodes can securely execute computationally intensive tasks off-chain and then submit the results on-chain. Applications can therefore offload computational overhead from the blockchain layer to the trusted off-chain environment. This helps lower gas costs and boost the overall throughput of the chain.
IExec is a major decentralized cloud computing platform using Trusted Execution Environments for off-chain computations. It utilizes Intel SGX-based enclaves to offload and isolate computation from the blockchain.
A requester, typically a smart contract or a user, can request a confidential computation as a task on-chain. The blockchain then notifies worker nodes to complete the task within a secure enclave. Before execution starts, the enclave produces an attestation report containing cryptographic evidence of the enclave’s code and configuration.
This report is then sent to a Secret Management Service, which verifies the integrity and authenticity of the enclave. Actual computation only begins if the enclave passes this verification.
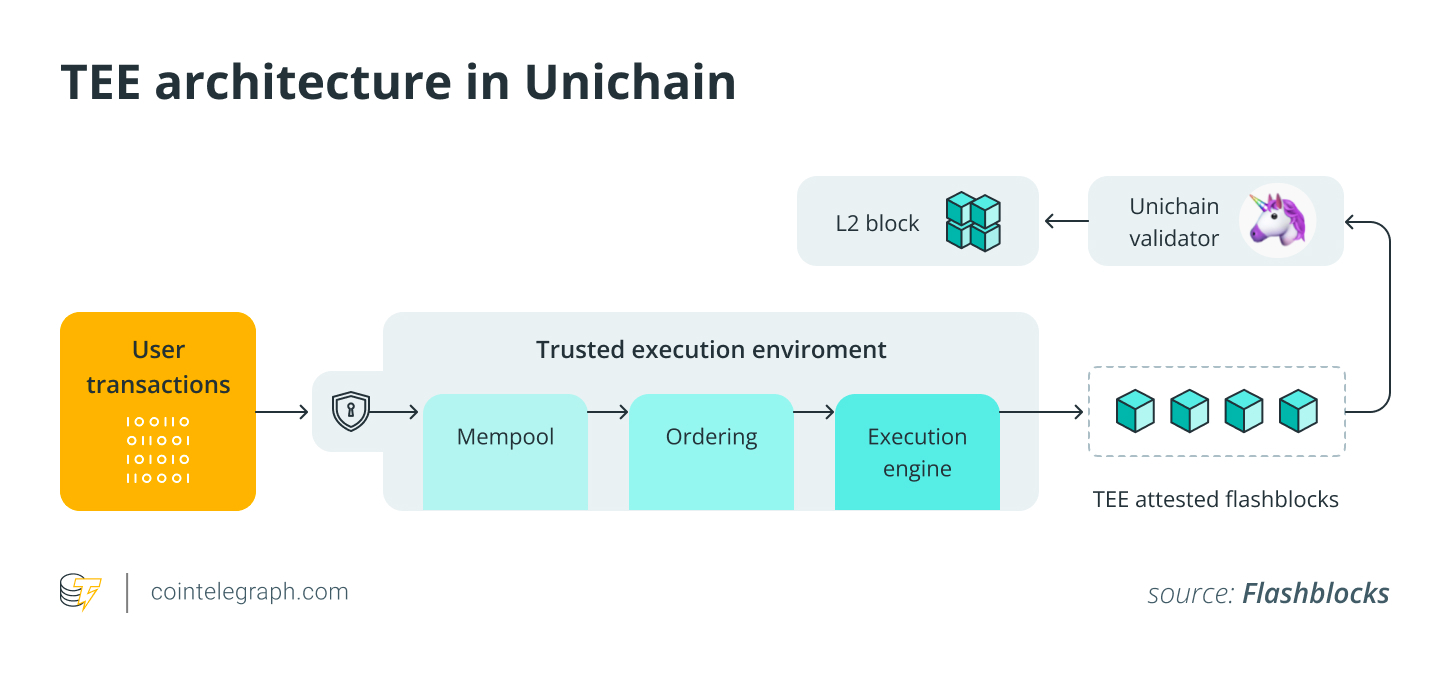
Trusted execution environments can also support MEV-resistant blockchain infrastructure. Unichain, an optimistic rollup on Ethereum, was developed by the Uniswap team and launched in October 2024. It uses TEEs in its block-generation process. The block builder, created with Flashbots, uses TEEs to assemble blocks inside a protected enclave.
When transactions are sent to the TEE builder, they are filtered, prioritized, and bundled into Flashblocks. This enables Unichain to achieve one-second block times, with plans to introduce 250-millisecond sub-blocks and enhance transaction ordering. Building blocks within TEEs reduces MEV extraction because mempool transactions remain encrypted. Through these capabilities, Unichain intends to establish a DeFi-focused blockchain.
In Conclusion
Trusted execution environments in blockchains are gaining traction as developers seek more effective privacy solutions. TEEs offer potential in shaping the future of decentralized applications by providing secure computation at low costs and high throughput. Despite their promise, most blockchains don’t currently natively support TEEs due to hardware requirements and the trust assumptions involved.
Looking ahead, we anticipate that TEE applications will expand beyond privacy-focused applications and concentrate on scalability solutions for blockchains and off-chain computation for decentralized applications. This trend is spurred by the growth of more computationally demanding DApps, such as decentralized AI applications. TEEs can support these applications through affordable, high-performance off-chain computation.
This content is intended for informational purposes only and does not constitute financial advice. Investing involves risk, and you should perform your own due diligence before making any decisions.
This article provides general information and should not be considered legal or investment advice. The views expressed belong solely to the author and do not necessarily reflect the opinions of Cointelegraph.
Cointelegraph does not endorse the content of this article or any products mentioned. Readers should conduct their own research before taking any action related to any product or company mentioned and are fully responsible for their decisions.

