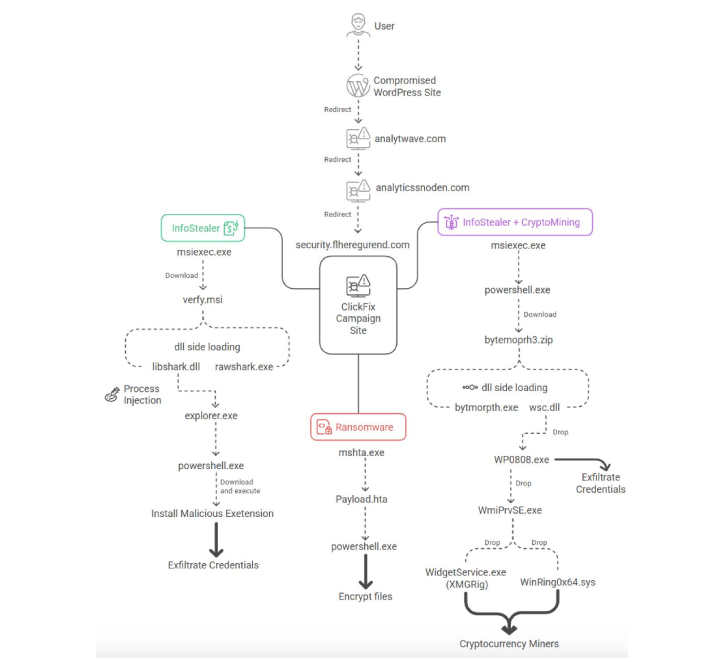
A widespread malicious campaign is underway, leveraging over a hundred compromised WordPress websites. This campaign redirects visitors to deceptive CAPTCHA verification pages. These fraudulent pages utilize a social engineering method known as ClickFix, ultimately delivering information-stealing malware, ransomware, and cryptocurrency mining software.
This expansive cyberattack, which emerged around August 2025, has been dubbed ShadowCaptcha by the Israel National Digital Agency.
“This campaign employs a combination of social manipulation, the use of legitimate system tools for malicious purposes (LOLBins), and a multi-stage delivery process to infiltrate and maintain control over targeted systems,” stated researchers Shimi Cohen, Adi Pick, Idan Beit Yosef, Hila David, and Yaniv Goldman in their report.
“The primary goals of ShadowCaptcha include harvesting sensitive information through credential theft and extracting browser data, deploying cryptocurrency miners for illicit gains, and even initiating ransomware attacks.”
The attack sequence starts when unsuspecting users visit a WordPress site that has been infiltrated with malicious JavaScript code. This code initiates a chain of redirects, leading victims to a fake Cloudflare or Google CAPTCHA page.
From this point, the attack diverges into two paths, determined by the specific ClickFix instructions displayed on the deceptive webpage: one route exploits the Windows Run dialog, while the other instructs the user to save the page as an HTML Application (HTA) and then execute it using mshta.exe.
The path initiated through the Windows Run dialog culminates in the deployment of Lumma and Rhadamanthys information stealers. This is achieved either via MSI installers launched using msiexec.exe or through remotely hosted HTA files executed using mshta.exe. Conversely, executing the saved HTA payload leads to the installation of Epsilon Red ransomware.
Notably, the utilization of ClickFix techniques to deceive users into downloading malicious HTA files for the purpose of spreading Epsilon Red ransomware was previously reported by CloudSEK last month.
“The compromised ClickFix page automatically runs obfuscated JavaScript code that uses ‘navigator.clipboard.writeText’ to silently copy a malicious command to the user’s clipboard, relying on the user to unknowingly paste and execute it,” the researchers explained.
These attacks are characterized by the implementation of anti-debugging techniques to thwart inspection of web pages using browser developer tools. Furthermore, they leverage DLL side-loading to execute malicious code while disguised as legitimate system processes.
Certain instances of the ShadowCaptcha campaign have been observed delivering an XMRig-based cryptocurrency miner. In some variants, the mining configuration is retrieved from a Pastebin URL instead of being hardcoded within the malware, enabling attackers to dynamically adjust parameters.
In cases where cryptocurrency miners are deployed, the attackers have also been observed introducing a vulnerable driver (“WinRing0x64.sys”) to gain kernel-level privileges and interact with CPU registers, aiming to optimize mining efficiency.
The majority of infected WordPress sites are located in countries like Australia, Brazil, Italy, Canada, Colombia, and Israel, and span various sectors including technology, hospitality, legal/finance, healthcare, and real estate.
The exact methods used to compromise these WordPress sites remain unclear. However, Goldman informed The Hacker News that there is a moderate level of confidence that attackers gained access through known vulnerabilities in various plugins and, in some cases, by exploiting the WordPress portal with compromised credentials.
To mitigate the threats posed by ShadowCaptcha, it’s crucial to educate users about ClickFix campaigns, implement network segmentation to prevent lateral movement, and ensure WordPress sites are regularly updated and secured with multi-factor authentication (MFA).
“ShadowCaptcha highlights the evolution of social engineering attacks into comprehensive cyber operations,” the researchers emphasized. “By deceiving users into executing built-in Windows tools and layering obfuscated scripts and vulnerable drivers, attackers achieve stealthy persistence and can switch between data theft, cryptocurrency mining, and ransomware deployment.”
This disclosure coincides with GoDaddy’s detailed analysis of the evolution of Help TDS, a traffic distribution system active since 2017 and associated with malicious schemes like VexTrio Viper. Help TDS provides partners and affiliates with PHP code templates that are injected into WordPress sites, redirecting users to malicious destinations based on predefined targeting criteria.
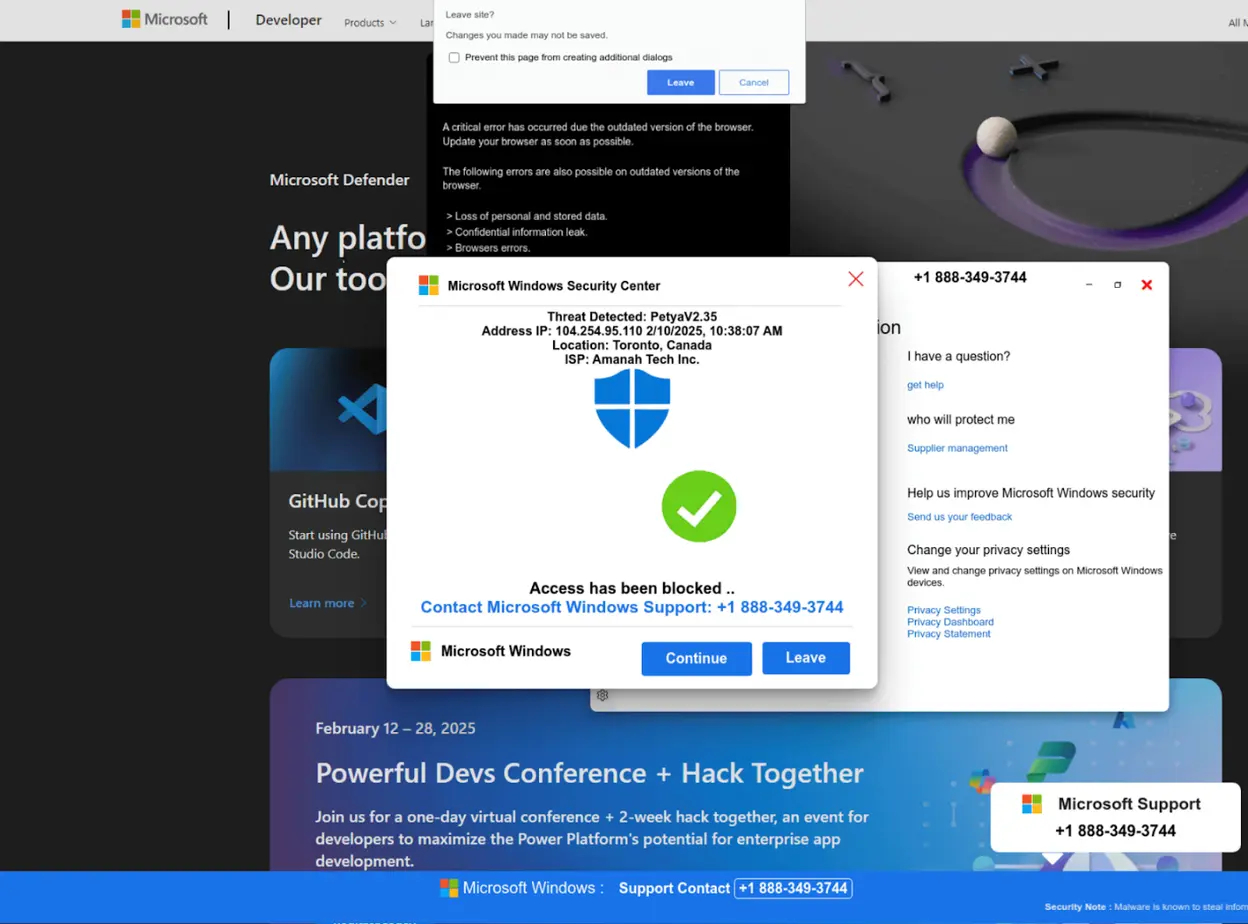
“This operation specializes in tech support scams that utilize full-screen browser manipulation and exit prevention techniques to trap victims on fraudulent Microsoft Windows security alert pages, with alternative monetization strategies involving dating, cryptocurrency, and sweepstakes scams,” explained security researcher Denis Sinegubko from GoDaddy.
Notable malware campaigns that have exploited Help TDS in recent years include DollyWay, Balada Injector, and DNS TXT redirects. These scam pages employ JavaScript to force browsers into full-screen mode and display fake alerts, even incorporating counterfeit CAPTCHA challenges before rendering the page to evade automated security scans.
Help TDS operators reportedly developed a malicious WordPress plugin, named “woocommerce_inputs,” between late 2024 and August 2025 to facilitate the redirection functionality. They have also consistently added credential harvesting capabilities, geographic filtering, and advanced evasion techniques. The plugin is estimated to be installed on over 10,000 websites globally.
This malicious plugin disguises itself as WooCommerce to avoid detection by site owners. Attackers exclusively install it after compromising WordPress sites, typically through stolen administrator credentials.
“This plugin serves as both a traffic monetization tool and a credential harvesting mechanism, showcasing a continuous evolution from simple redirect capabilities to a sophisticated malware-as-a-service offering,” stated GoDaddy.
“By offering ready-made solutions, including C2 infrastructure, standardized PHP injection templates, and fully-featured malicious WordPress plugins, Help TDS has lowered the barrier to entry for cybercriminals looking to monetize compromised websites.”