A widespread security breach has impacted commonly used JavaScript software building blocks, identified as a potentially record-breaking supply chain compromise. The malicious software injected is believed to be engineered to pilfer cryptocurrency by modifying digital wallet destinations and seizing control of transactions.
Multiple reports surfaced on Monday detailing how cybercriminals infiltrated the node package manager (NPM) profile of a respected programmer and secretly integrated malicious code into prevalent JavaScript components utilized by a multitude of applications.
This harmful code substitutes or seizes control of cryptocurrency wallet details, possibly placing numerous projects at substantial risk.
“A large-scale supply chain attack is unfolding: the NPM account of a trusted software developer has been breached,” Ledger’s Chief Technology Officer, Charles Guillemet, alerted on Monday. “The compromised components have already been downloaded exceeding a billion times, indicating that the entire JavaScript environment is possibly vulnerable.”
The security incident specifically targeted libraries like chalk, strip-ansi, and color-convert—small but essential tools deeply embedded within the dependency trees of countless software projects. Combined, these components are downloaded well over a billion times per week, meaning even developers who haven’t directly installed them could be exposed to the threat.
NPM serves as a central repository for developers, similar to an app marketplace, facilitating the sharing and downloading of small code packages essential for constructing JavaScript applications.
It seems the perpetrators implemented a crypto-clipper, a specific type of malware designed to secretly replace wallet addresses during cryptocurrency transactions, thereby rerouting funds to the attacker.
Cybersecurity experts caution that users relying on software-based crypto wallets may be particularly at risk, while those who diligently verify each transaction on hardware wallets are more likely to be protected.
Caution Urged: Avoid Cryptocurrency Transactions
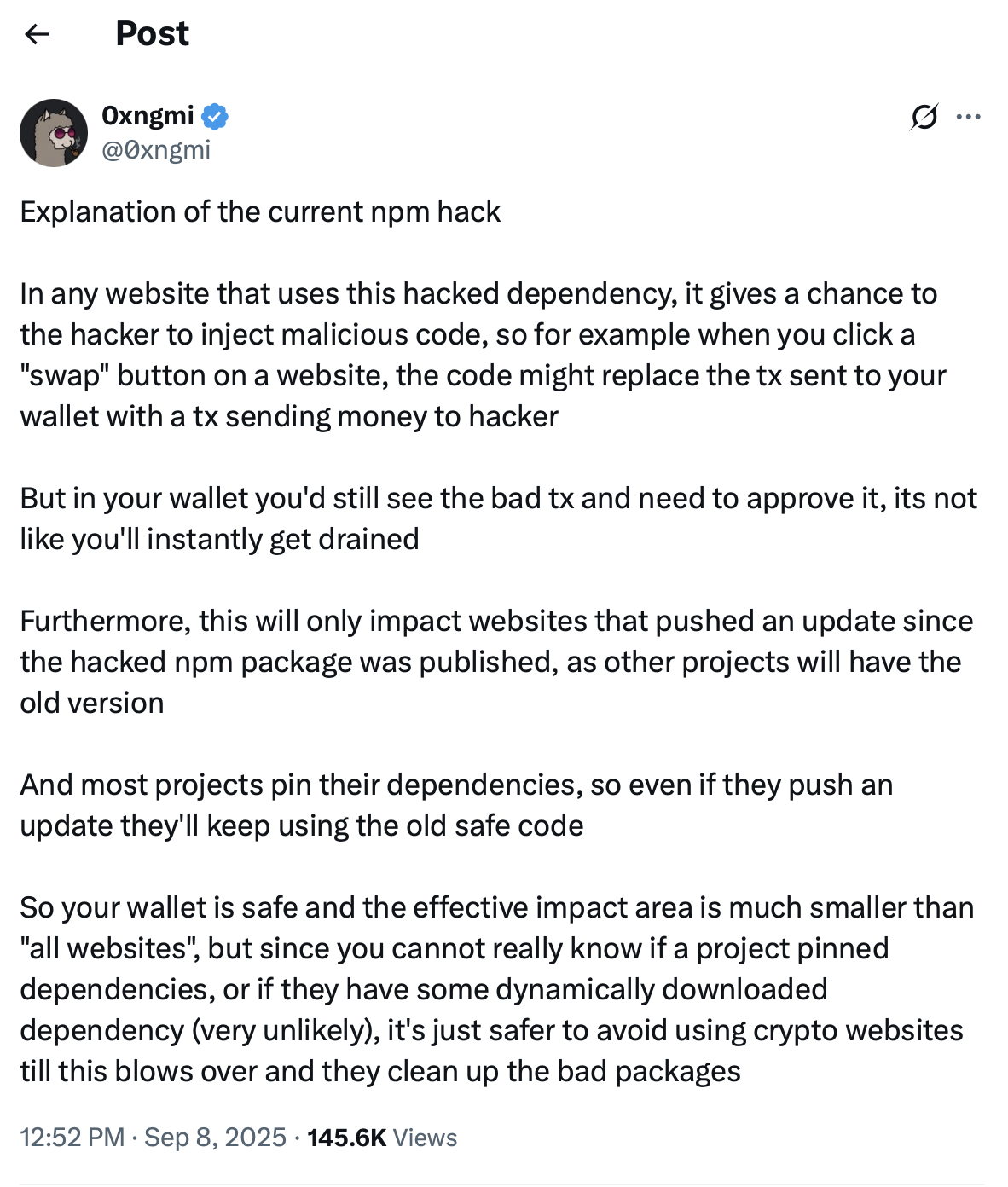
According to a statement on X by DefiLlama’s founder, Oxngmi, the malicious programming does not automatically empty digital wallets; individuals would still need to authorize a compromised transaction.
Given that the breached JavaScript package is capable of modifying button functions, clicking the “swap” button on an affected website could alter transaction details, redirecting funds to the attacker instead of the intended recipient.
He also pointed out that only projects that underwent updates after the contaminated package was made accessible are at risk, and numerous developers “pin” their dependencies, ensuring they continuously operate older, secure iterations.
Nonetheless, because users have difficulty determining which sites have been updated properly, it is advisable to refrain from engaging with cryptocurrency websites until the impacted packages have been sanitized.
Phishing Scheme Granted Access to NPM Accounts
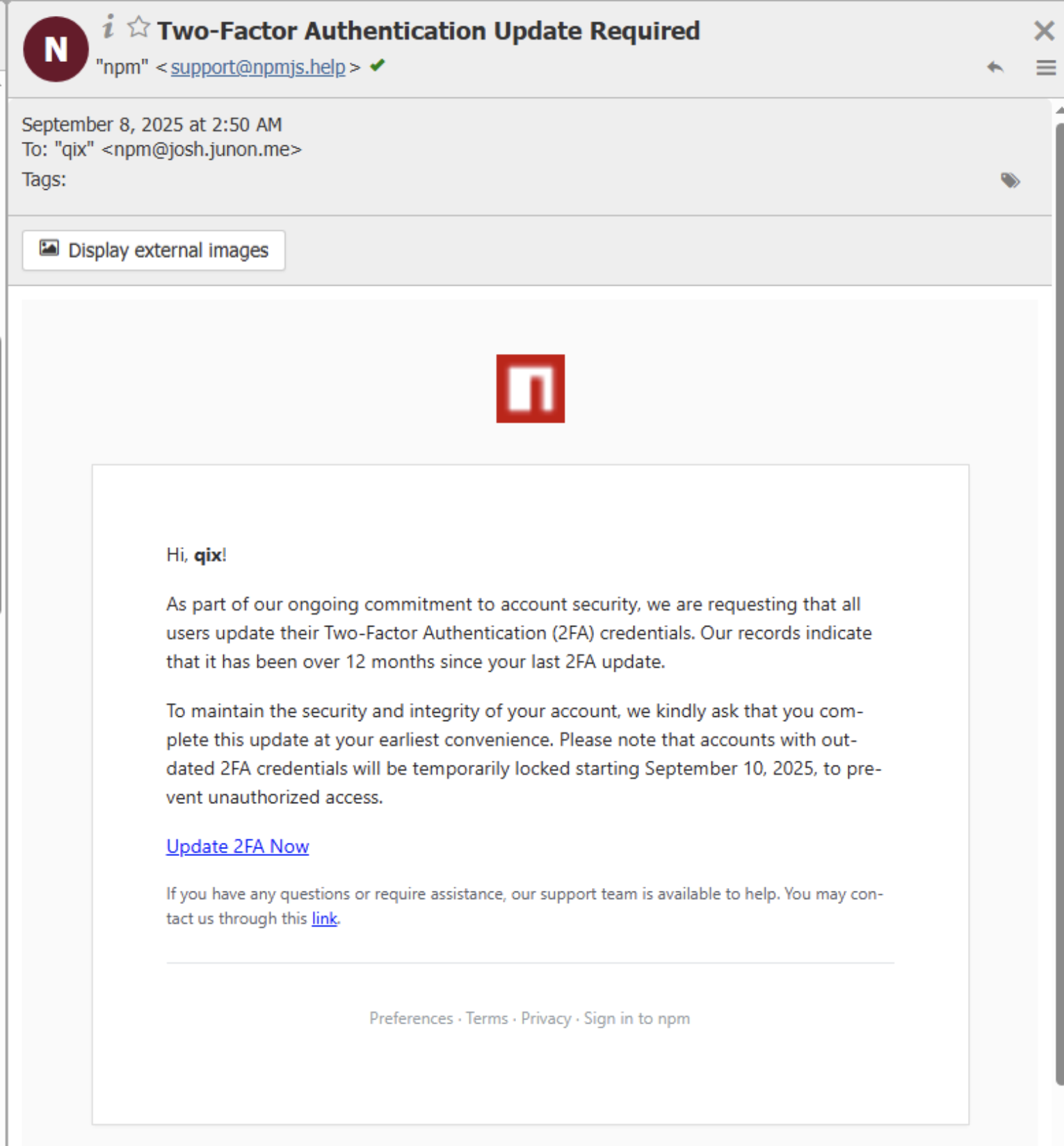
The attackers launched a phishing campaign utilizing emails disguised as official NPM support correspondence. These emails cautioned maintainers about impending account suspension unless they purportedly “updated” their two-factor authentication by September 10.
This fraudulent site collected user login information, enabling attackers to take control of the maintainer’s accounts. With this access, the attackers then issued infected updates to packages that see billions of downloads each week.
Charlie Eriksen, a security researcher at Aikido Security, explained to BleepingComputer that the attack proved particularly concerning due to its multi-layered nature, including “altering content shown on websites, tampering with API calls, and manipulating what users’ apps believe they are signing.”
Magazine: Inside a 30,000 phone bot farm stealing crypto airdrops from real users

